Issues encountered post deployment of Netscaler 10.5
Requirement:
Customer imported NetScaler 10.5 VPX to Hyper-v and requested us to configure further configurations
Issue 1:Netscaler URL is not opening over internet
Observations & changes done:
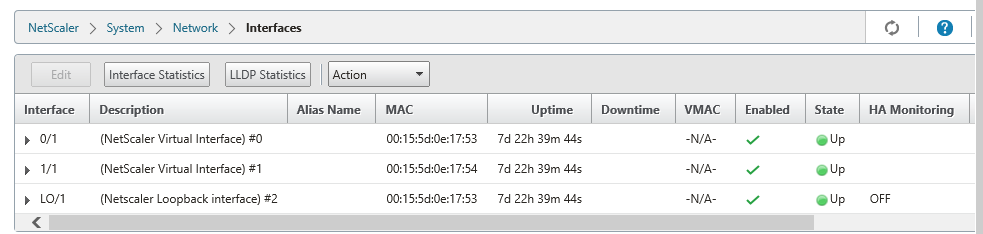
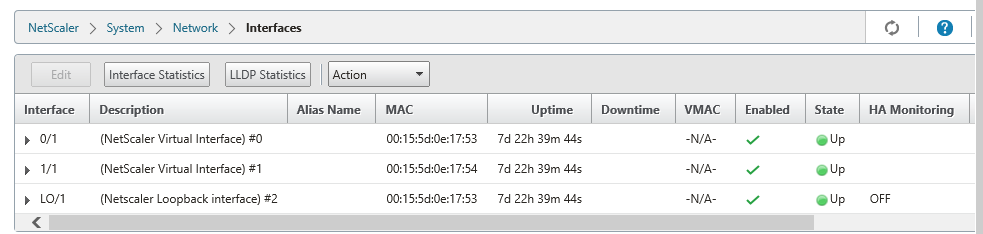
Netscaler has 3 Interfaces ( DMZ, LAN Zone & Loopback)
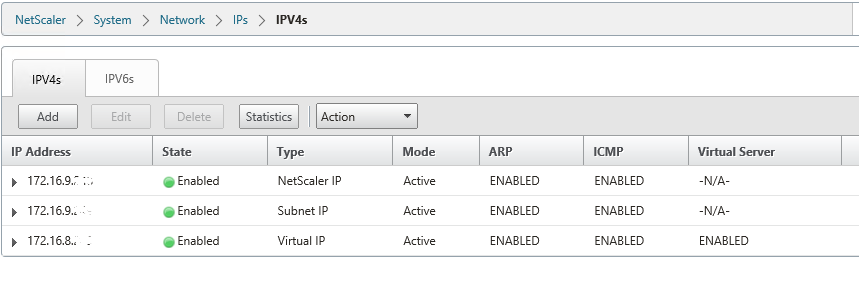
Netscaler IP’s as below
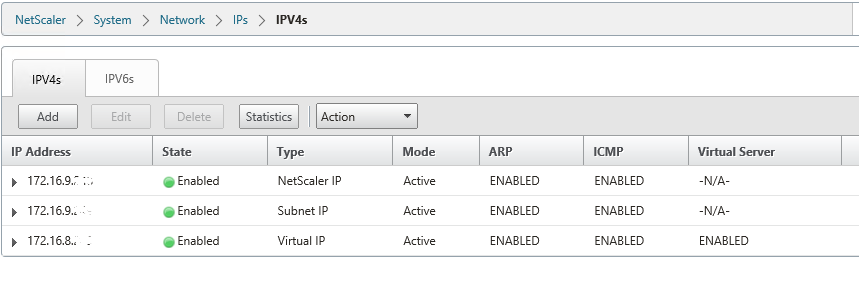
- 172.16.8.X is DMZ Virtual IP. It should be properly natted to public IP 192.X.X.X, then only Netscaler Access gateway web page will open over internet.
- Network Team will do internal routes from 172.16.8.X to core switches so that it will reach to Citrix infra servers
- Note that ,172.16.8.x is the virtual IP which you will configure in Gateway virtual server
- Make sure that 80(STA Port),443(STA Port) ,1494 & 2598 ports opened bidirectional from Netscaler Virtual IP(172.16.8.X) to Citrix infrastructure servers
After above configurations, netscaler web page opening over internet but observed certificate errors and Authentication issue
Issue 2:
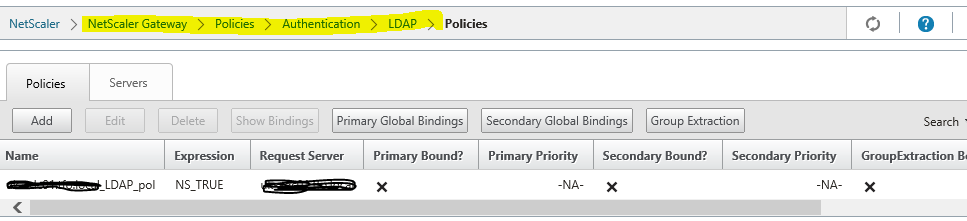
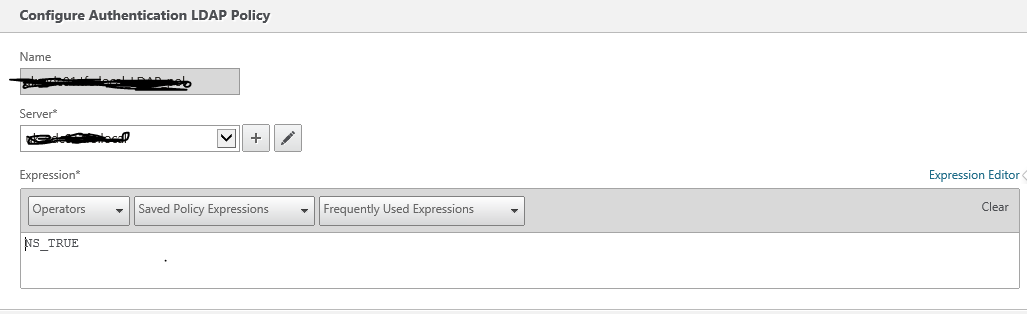
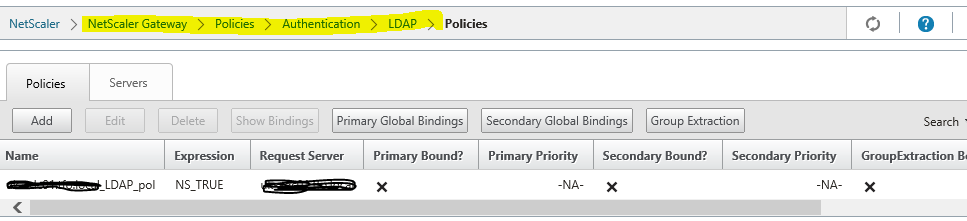
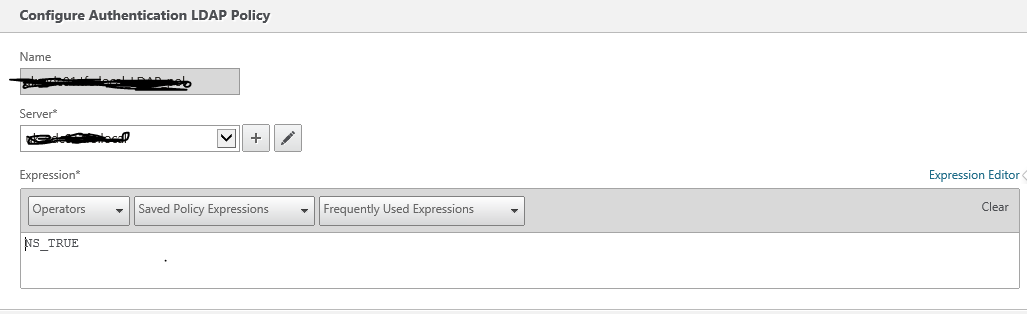
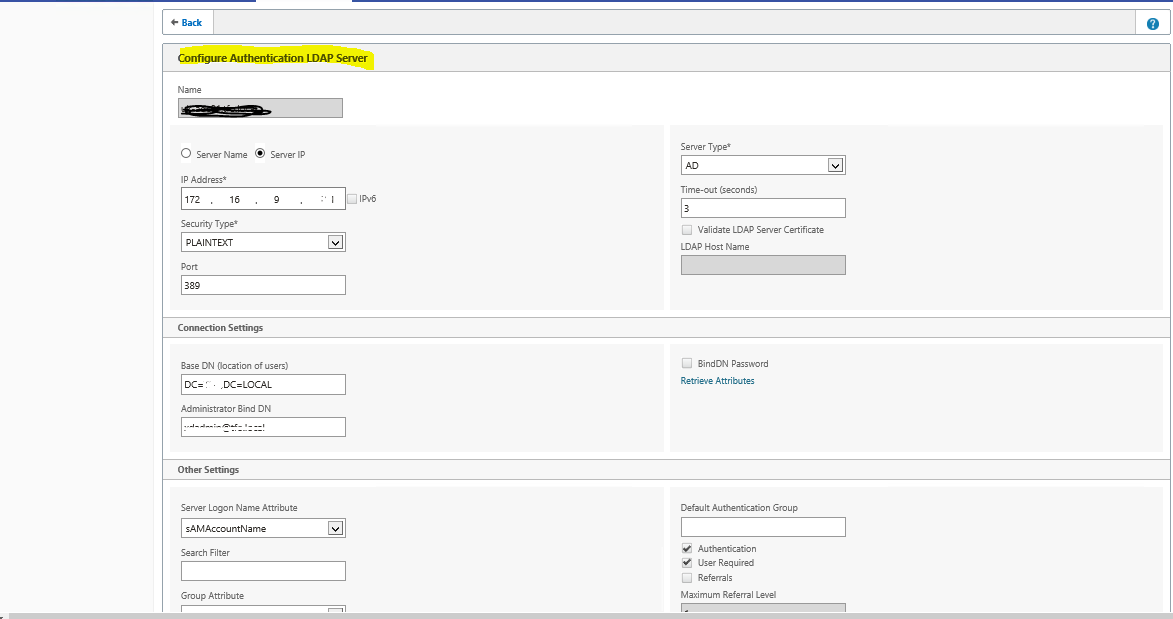
User getting error that the credentials are incorrect when logging to Netscaler
Resolution:
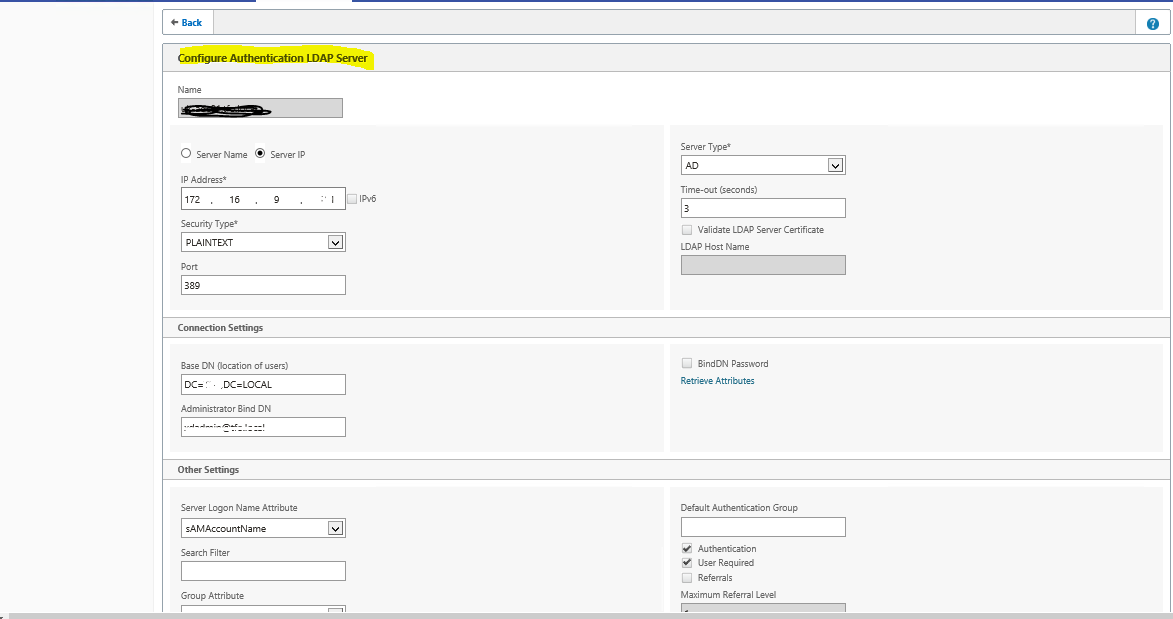
The LDAP configuration was not as per the article http://support.citrix.com/article/CTX108876 correcting which rectified the behavior of incorrect username password.
Issue 3: Certificates errors on Netscaler.
Observations & changes done:
- Observed intermediate & root certificates are missing in NetScaler which creating authentication issues too..
- From Client end they are able to get authenticating prompt but not able to get establishing the full session
- Using the openssl command we have verified that the certificate chain is complete and linked on the VPN virtual server on Netscaler Gateway.
- # /usr/bin/openssl s_client -connect <ip:port> -showcerts
As per article http://support.citrix.com/article/CTX114146
Issue 4:
VDI launching is working with internal URL and not working externally, throwing VDI error
Observations & Changes done
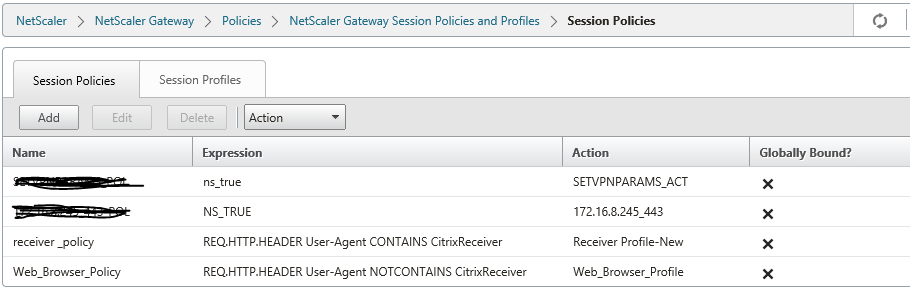
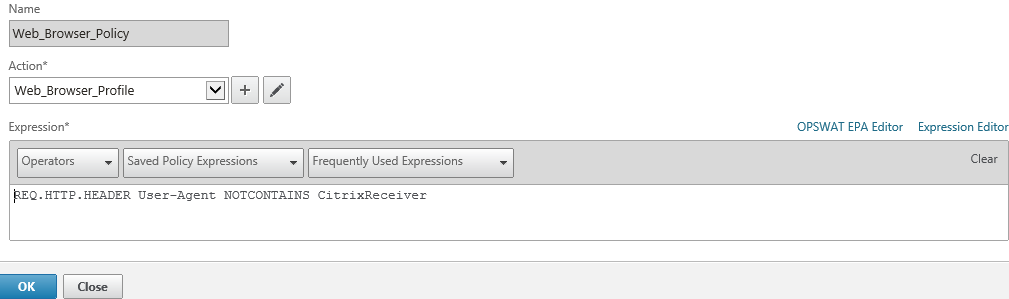
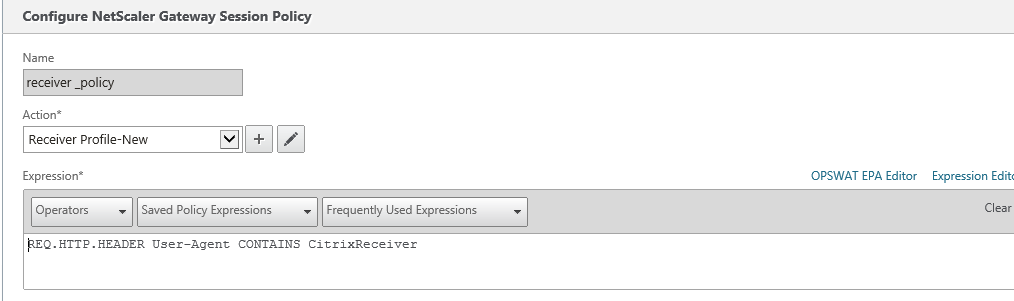
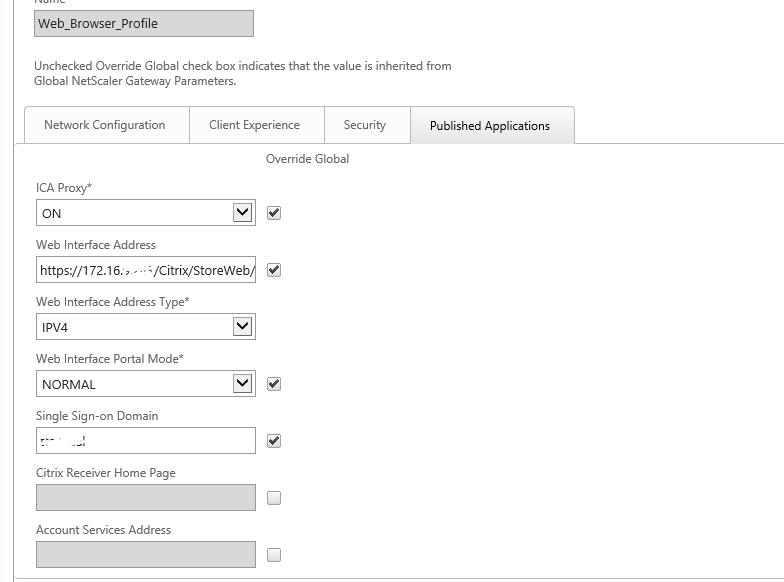
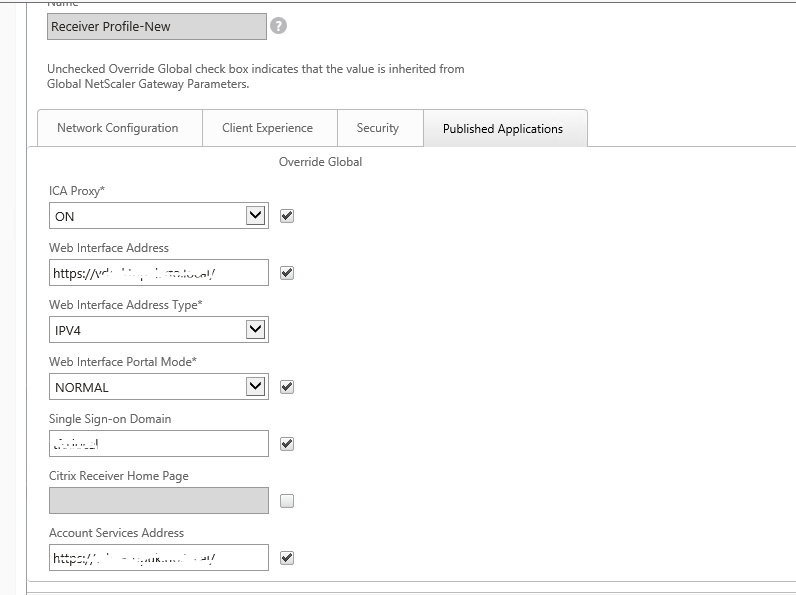
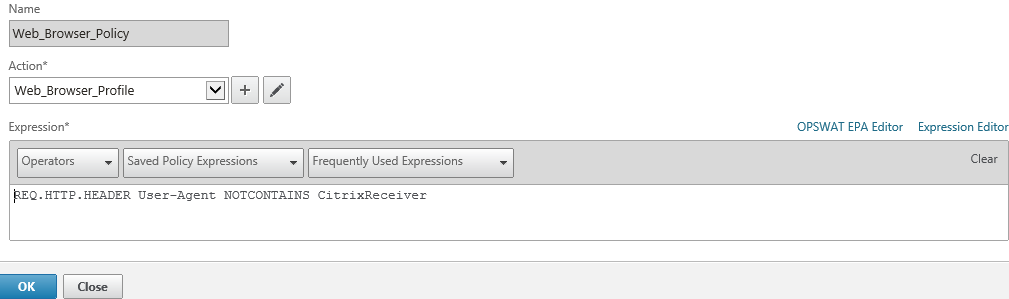
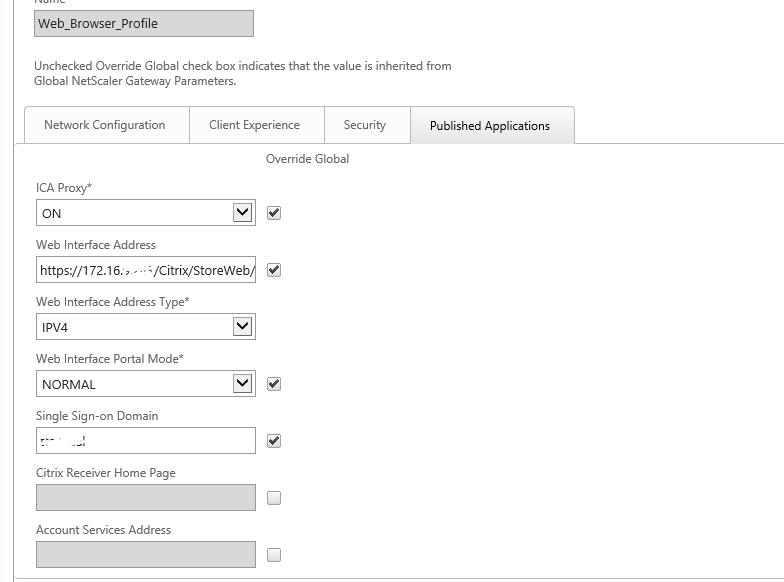
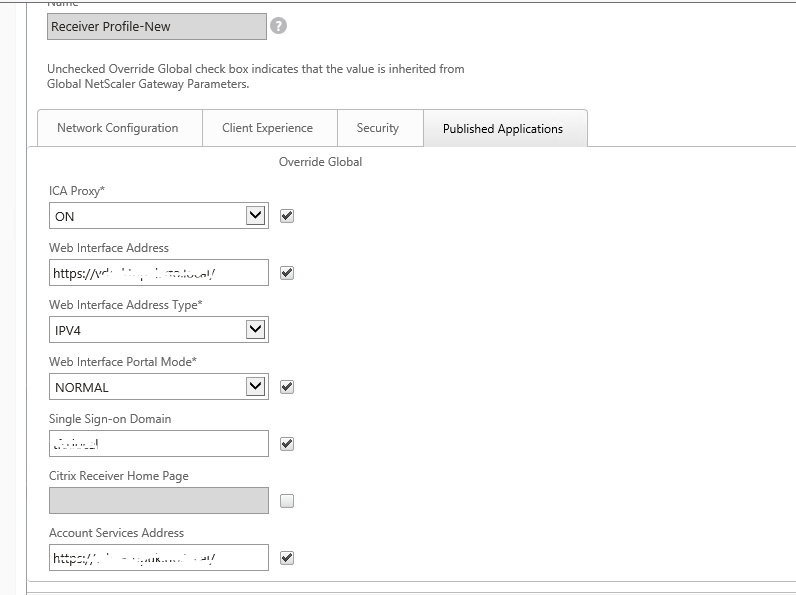
- Observed session polices were incorrectly configured, created 2 session policies (Web & Receiver Policy)
Using the article http://support.citrix.com/article/CTX139963
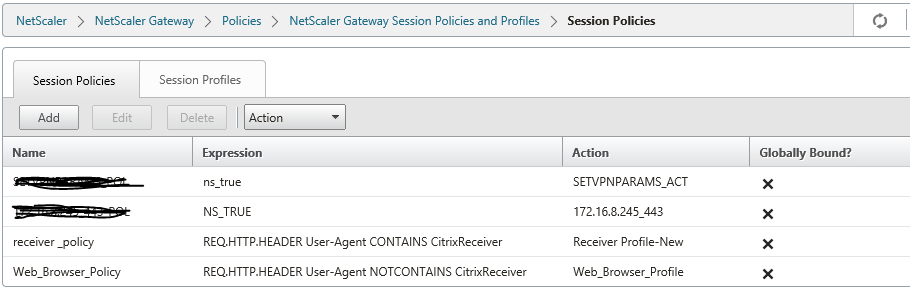
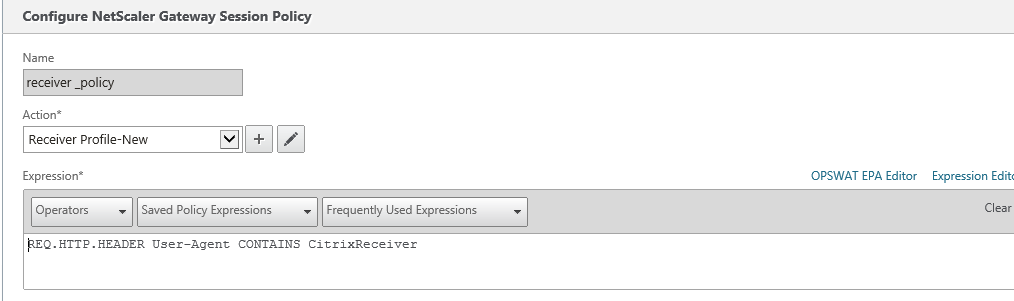
For Receiver, need to configure account services address (Similar to Xenapp Services URL)
Issue 5:
Error: Cannot complete request, before log into Netscaler webpage and issue is same from internal URL too.
Observations:
- Load balancing Virtual name(VDIDesktopxx.locaL) is configured in Session profile but these load balancing VIP (SF1+Sf2) were hosted on separate load balancer and there was some issue with load balancing VIP
- Customer removed Storefront load balancing IP configuration , informing us to point one storefront(SF1) only in Netscaler.
- Post Load balancing configuration removal, we got the error “Cannot complete request” as netscaler is unable to find the load balance IP
Changes done:
- Certificate was binded with local load balancing virtual name(VDIDesktopxx.locaL) hence to maintain the same , we created alias entry for SF1 server so that same URL will be accessed internally and the same reachable from netscaler
- Observed XML was set to false in DDC, recommended to make it true so ran the command set-brokersite -TrustRequestsSentToTheXmlServicePort $true
After doing all above changes, Users are able to launch VDI externally and internally without any issues