Citrix Desktop As a Service (DaaS) vs Microsoft Azure Virtual Desktop(AVD)
In this blog, I would like to share my thoughts on Citrix DaaS and AVD with respect to Architectures, Features, Security, Cost , Benefits of using both products together etc..
I collected information from multiple blogs and added my real-time experience skills for simplification.
Thanks to sandbu
- Architecture
- Technical Features & Offerings
- Management (Flexibility, Image Management, Automation, Monitoring)
- Security
- End User Experience
- Cost
- Benefits of Citrix with AVD
Architecture
This section is meant just to provide some context around the overall architecture of both platforms and their services
Citrix DaaS (Desktop As a Service)
Much of the services that Citrix have been building over the last years have been around their managed cloud service called Citrix Cloud. This service provides much of the functionality needed to manage, provision, and provide connectivity to the infrastructure using a local component called Cloud Connector. The Cloud service itself is built on top of a combination of AWS and Microsoft Azure to run
Their management plane is delivered in 5 different regions (US, US-GOV, EU, JAPAN, Asia Pacific South) so when you create a management plane tenant you need to select one of these regions. This means that all APIs/changes/updates need to go to that region. Much of the Citrix Cloud services are running on Microsoft Azure, as can be seen as part of the FQDN documentation here –> System and Connectivity Requirements | Citrix Cloud
Regarding the data plane (handling user session connections to the actual VDI/VDA), this can either be done using on-premises Gateway appliances or their managed data plane service called Gateway-as-a-service.
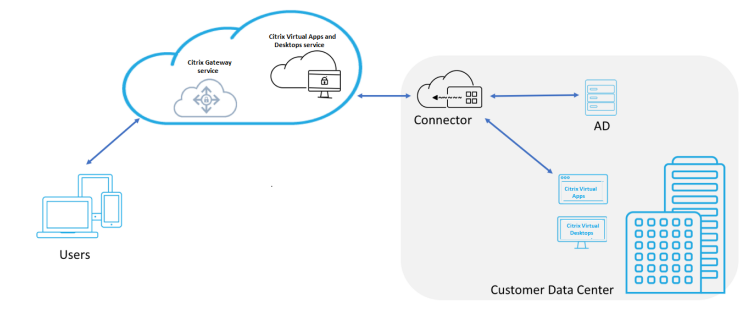
This connection point supports a UDP-based connection using a protocol called EDT which is based upon DTLS (This requires the use of the Rendezvous protocol, more about that part a bit later)
This means that traffic coming from an end-user is going to one of the POPs (Point of presence) that Citrix has –> Citrix Gateway Service – Points-of-Presence (PoPs) then being redirected to the VDA. The service is behind a DNS load balancing capability which redirects the user to the closest PoP location.
The connection to the infrastructure is done via a virtual machine that hosts the cloud connector service, (Citrix Gateway Connector) which acts as the connectivity proxy for VDAs and Citrix Cloud. Also depending on which feature of the protocol is used –> Rendezvous protocol | Citrix DaaS the Cloud Connector also acts as a proxy if the Rendezvous protocol is not used for connectivity.
The users connect to the Citrix Cloud Workspace service which acts as a user interface and connection point when users want to start an application or desktop. The workspace can be configured to be integrated with different identity providers, either Azure AD, SAML, Active Directory, or on-premises Gateway.
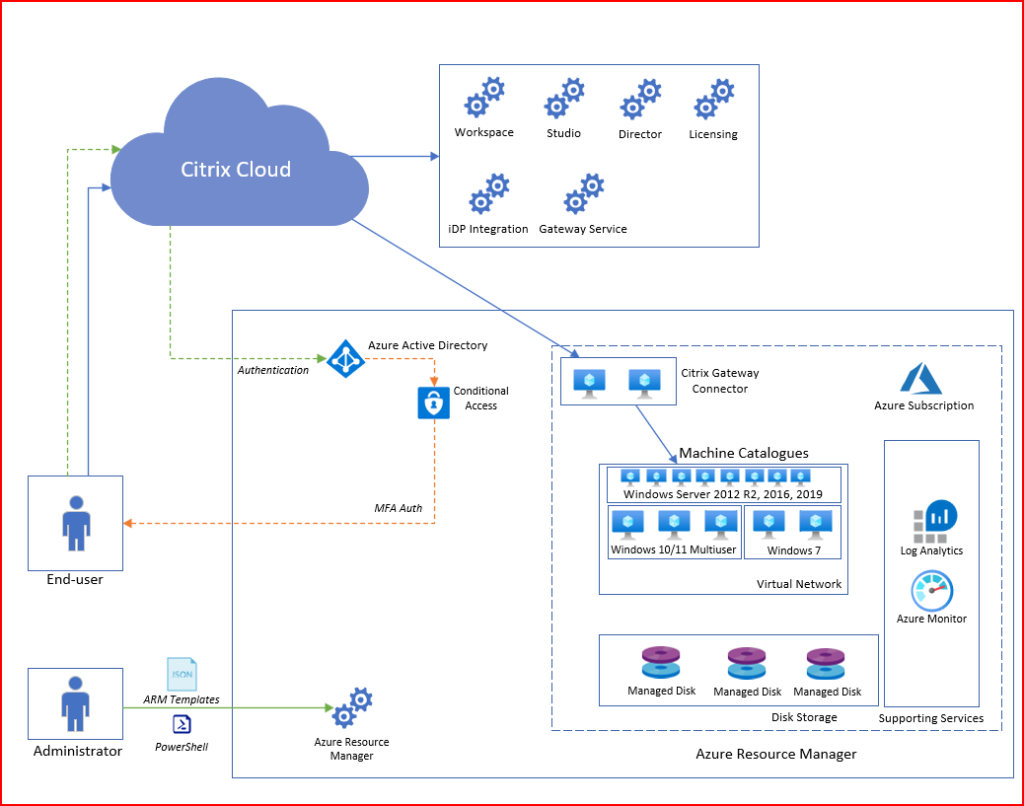
Microsoft Azure Virtual Desktop (AVD)
Microsoft’s AVD service is a bit simpler since it only consists of the AVD core components (That can be both a good and bad thing) more about that later. AVD consists of the PaaS services running in Azure. These are:
- Connection Broker
- Gateway
- Web Interface
- Diagnostics
- Licensing
All these services are mostly globally available, and load-balanced using Azure Front door to provide redundancy and route users to the closest region. The service is configured from a customer tenant and managed within Microsoft Azure as a native Resource Manager Service.
From an administrator perspective, you have the AVD Workspace where you configure Host Pools and Application Groups which are the only part that you can configure and manage for the AVD service. Logs and metrics are collected from the AVD Workspace and host pool into Azure Log Analytics which provides data into the monitoring capabilities in Azure.
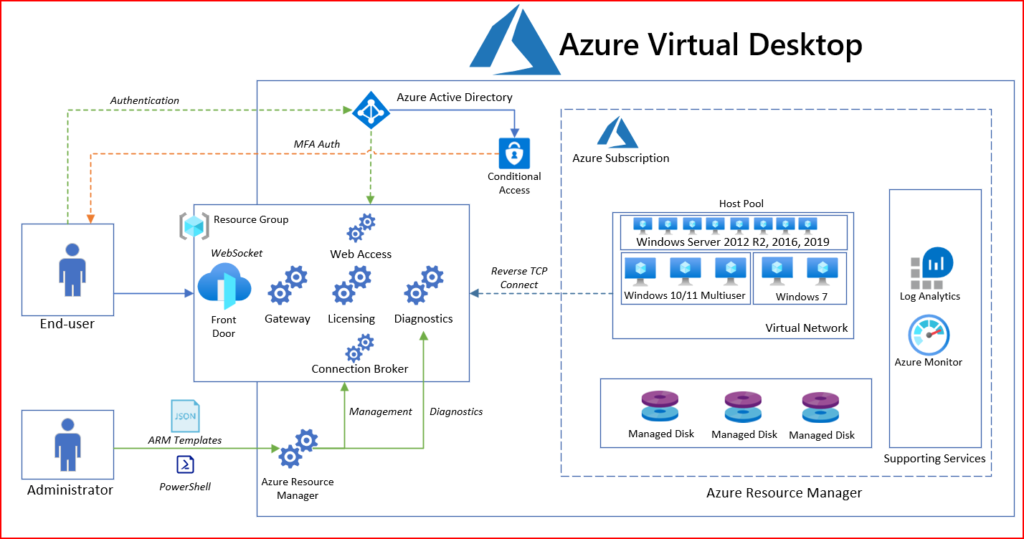
When users authenticate to the service you firstly have the Connection Broker which handles the session and authentication which uses Azure Active Directory-based authentication.
Then the RDagent on the backend machine will receive the session that was initiated the session which will then handle the authentication and data traffic.
With AVD we have the RDAgent installed on each machine that we want to deliver apps and desktops which is then associated with an AVD host pool that is unique for each tenant. That way the AVD service knows which AVD host pool to send traffic to once a user initiates a session.
Depending on what kind of protocol is used the RDAgent will either establish a session using a Reverse-TCP connection or use a Short Path Connection that uses UDP.
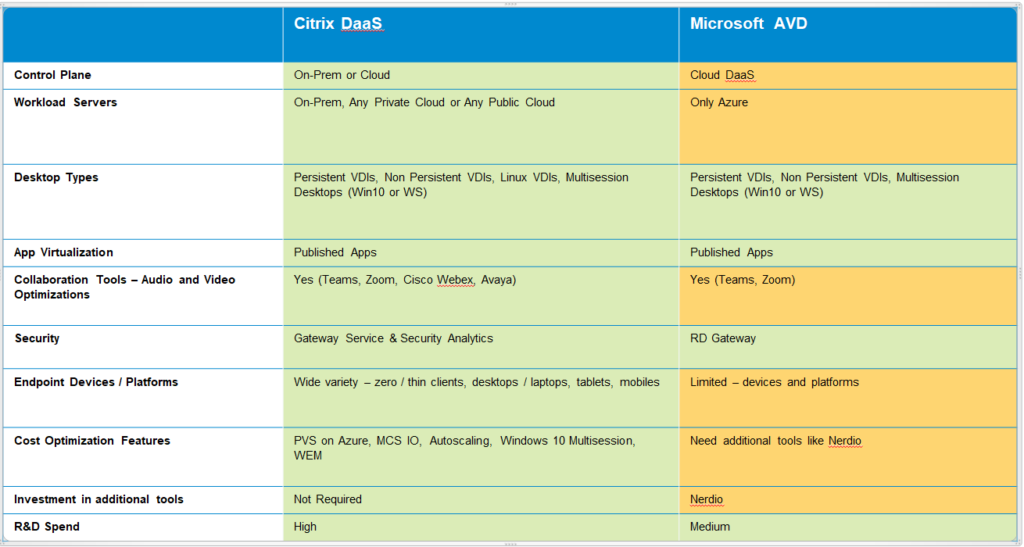
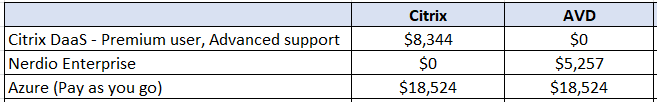
Technical Features & Offerings ( As on Dec-2022)
Management
Citrix
Management of Citrix is done via Citrix Cloud, either using the Web UI or using REST API (or PowerShell Module). The UI provides mechanisms to provision machines using MCS (Machine Creation Services) and assigning access to users and groups, this can be integrated with any cloud or on-premises hypervisor.
While MCS is integrated into the Cloud-based management, other provisioning mechanisms with PVS are managed through traditional VM-based management consoles (and are also supported on most clouds)
Citrix also has monitoring integration with Citrix Director that provides an overview of connection services and sessions which will come back in the monitoring section
Management can be configured granularly so that administrators can have customized access to the management plane and monitoring plane.
Microsoft
AVD Management is done using the Azure Management Plane (Azure Resource Manager). Administrators can either use the Azure Portal, Azure CLI, or IaC (ARM, BICEP, Terraform, or other options available)
In terms of Monitoring, data and events are being collected into Azure Log Analytics which are then visualized using Azure Monitor Workbooks.
Management in Azure is done granularly so access can be given to different resources and using just-in-time access with services like Azure Privileged Identity Management.
Flexibility
AVD uses a simpler architecture that runs both the control and data planes as Azure host services, meaning that customers only need to operate the VMs. Citrix customers can also use CVAD against multiple cloud platforms simultaneously, while also enabling business continuity and disaster recovery. AVD only supports Azure, but it has no known limits on its scalability.
CVAD can integrate with many on-premises platforms like Citrix Hypervisor and VMware vSphere as well as cloud platforms such as Amazon Web Services (AWS), Google Cloud, and Microsoft Azure. It also offers greater flexibility than AVD in terms of deployment options, especially with respect to Active Directory (AD) structures, traffic steering, and double-hop support
Image Management
AVD doesn’t currently have its own ability to manage images, but administrators do have other means of obtaining this capability since AVD is native to Azure. For example, they can use Azure Image Builder (AIB) for this purpose or Azure Computer Gallery, which allows admins to automate the creation of Azure VM images by using configuration files. AVD can’t automatically provision VM based on a new image because Image Builder isn’t natively integrated to AVD. However, AIB & Azure Computer Gallery is a generic Azure service, so admins can combine it with other services to build an image.
Admins can facilitate image management with CVAD by using both Machine Creation Services (MCS) and Provisioning Services (PS). MCS uses storage to clone and provision VMs, while PS uses network-based image streaming to provision VMs.
Application Delivery
The delivery of application functionality for AVD is comparatively limited when considering it by itself. However, the Azure ecosystem includes other capabilities that users can combine with AVD to access additional applications. For example, Azure AD Application Proxy allows access to web applications that are part of Azure AD. The only disadvantage of this method of application delivery is that users must access AVD and these applications from two different portals.
CVAD provides access to other OSs like Linux in addition to the web-based applications integrated into their gateway components. This capability also provides remote access to computers via their remote PC functionality. In addition, CVAD includes always-on virtual private network (VPN) capabilities for applications and services. Azure offers this capability as well, although separately from CVAD itself.
Automation
If organization have already adopted DevOps / IaC against Microsoft Azure, you will be able to manage most of the AVD setup, image management and operations using the same set of ecosystems. There are also already many good examples on how you can use Terraform to configure and manage much of the AVD environments.
With the simplistic nature of AVD being just an agent it is easy to onboard when needed using IaC. This means that you can manage the entire platform using the same set of automation tools.
This is unfortunately not the same for Citrix, where you will need to use PowerShell or REST APIs to manage the same. There are of course some modules available for NetScaler, but not for the core Citrix management capabilities.
Monitoring
Microsoft had built monitoring capabilities of AVD based upon logs that are collected into Log Analytics from the AVD components and logs running on the virtual machines, which of course is not real-time based logging and might therefore not give the full spectrum.
However, if you have started to invest into the ecosystem of Azure including Azure Sentinel, it can provide a wide range of detection mechanisms against AVD hosts and the management plane.
Still, I would have loved for AVD to have some more proactive monitoring capabilities for their services, relying on just the status page and log collection is still not good enough.
In terms of monitoring (and with that I mean real-time) Citrix has a much broader range of real-time statistics including deep insight into the different streaming channels to give insight into (what is hogging up the resources or bandwidth?)
Security
Citrix provides extensive enterprise security features, including FIPS compliance, Common Criteria certification, Microsoft Credential Guard compliance, multi-factor authentication, smart card integration, ICA proxy, and more. However, WVD provides adequate security measures based on the strong security features of the Azure cloud.
Windows Virtual Desktop
Includes security features like Reverse Connect, a secure virtualization control plane, security for physical hosts, the physical network, and the physical datacenter. However, Azure emphasizes customers need to take responsibility for identity and access management, user device protection, application security, session host operating system security, correct deployment configuration, and network controls.
Citrix
Citrix provides analytics that helps reveal unusual behavior or malicious access to desktops. You can apply Citrix Policies to enable or disable any functionality, and limit application access based on context with Citrix Cloud. Citrix provides a Secure Browser for locked-down access to specific SaaS applications.
Both vendors provide secure access to their services and a secure management plane. Both offerings can integrate with Azure AD and use conditional access policies to ensure that end users can only have access from certain devices and locations or if Azure AD deems the sign-in as low risk. Another interesting addition is that Citrix provides anti-keylogging and anti-screen capturing capabilities, which is something that WVD currently has in its roadmap but is not yet generally available.
One thing that turns security in Citrix’s favor is its analytics engine, which essentially monitors end-user behavior in real time and uses machine learning to monitor user risk. This could detect insider risks or if someone managed to access a legitimate user account and tried to obtain private information or data that they shouldn’t be able to access. This type of real-time insight into user sessions is not something that Microsoft currently has with WVD, but once again, WVD can bolster its feature set with Azure AD.
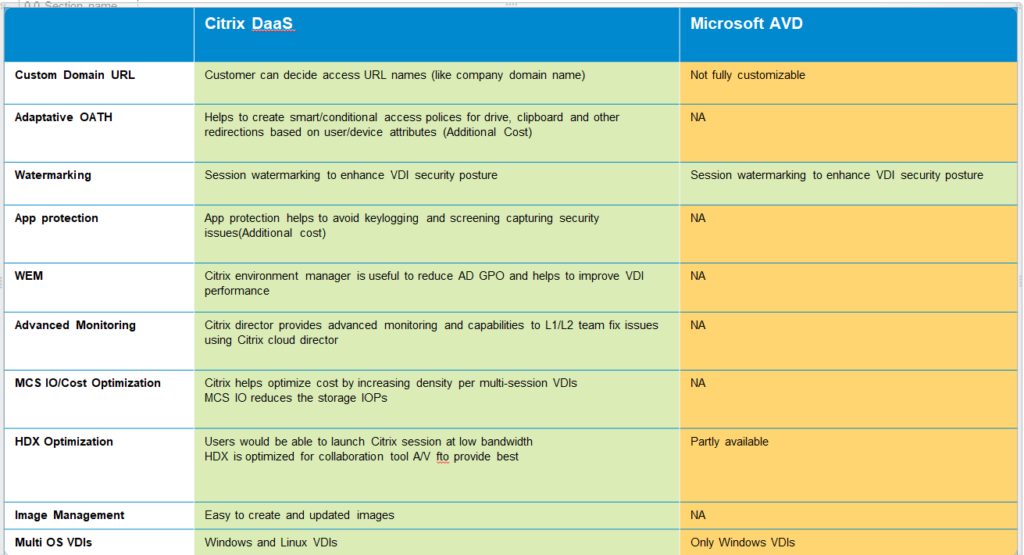
End User Experience
Looking at both vendors, they each provide a web-based and desktop client to access the environment. However, when it comes to SSO, Citrix is a bit ahead of the game — especially when it comes to Azure AD. WVD only supports Azure AD SSO through AD Federation Services ( Note: As on today Azure AD Seamless SSO is in Public Preview), while Citrix does this through its Federated Authentication Service (FAS) component. Citrix’s FAS essentially enables Windows 10 clients connected to Azure AD to authenticate via SSO directly into their desktop or application using that identity integration.
The second aspect is the network protocol. Both vendors provide a gateway service, which essentially means that IT has to route the traffic through their service and then to the back-end VDI or session host. However, WVD still only supports TCP-based connections (Note: RDP Shortpath is in Public Preview, RDP works on UDP), while Citrix HDX supports TCP and User Datagram Protocol-based transfers to provide a more fluent connection. Secondly, HDX is much more adaptive when it comes to bad network connections with high packet loss or high latency.
The last factor to consider is integration with peripherals and integration with local software, such as Microsoft Teams. WVD supports the same level of peripherals as Remote Desktop Services (RDS), which is somewhat on the same level as Citrix.
Cost
One of the biggest differences between Citrix and Windows Virtual Desktop is cost. AVD was designed as a low-cost solution.
AVD uses Azure’s own scaling model to charge customers only for the resources they use, making this cost an operational expenditure. CVAD generally requires customers to make a substantial capital investment for on-premises servers and licensing for Citrix’s own software as well as other software required by the servers such as Windows Server. As a result, CVAD is much more expensive than AVD, especially when it comes to upfront costs.
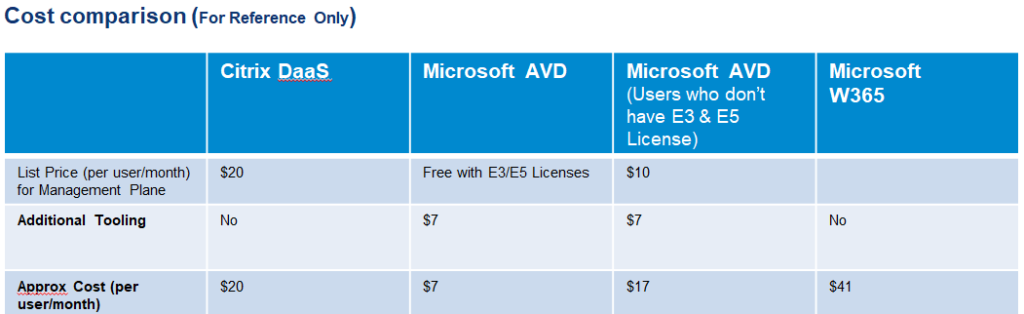
- Above data is taken from the vendors for reference purpose
- The above approx cost (per user/month) doesn’t include Azure consumption costs
- The table is primarily to simulate the cost options against Citrix & AVD technologies
- The above costs are indicated at respective list prices
For reference, find approx cost estimated for 750 users
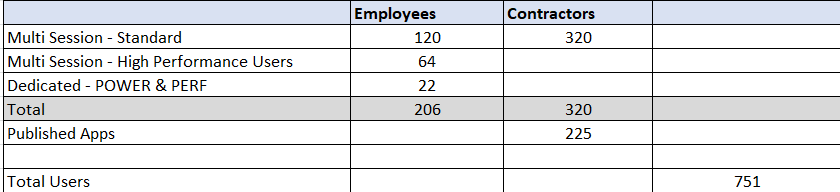
- With respect to list price Citrix is ~15% higher compared to AVD, but with discounts from Citrix this difference might reduce considerably
- Azure Pay as you go calculations are done considering 168 hours of usage/month
- Azure Reserved Instance (RI) will be higher by ~15% on pay as you go, but this will be beneficial if the user utilizes the VDI >200 hours/month
Benefits of Citrix with AVD
AVD itself is an ideal choice for many businesses (especially startups and small businesses). For large businesses, Citrix can extend Microsoft’s WVD, offering a management layer that increases flexibility, security and optimizes costs.
Why use Citrix and AVD together?
When you use Citrix on AVD, you still get access to the compute and licensing benefits of AVD, but in this scenario, you choose not to use the management and protocol that comes with AVD. Instead, you replace it with the Citrix-provided offering Citrix Virtual Apps and Desktops (CVAD).
The benefit of this option is that Citrix has 30+ years of development behind its tools. Their protocol and management plane support the more demanding requirements of some businesses in high-latency, high-loss situations and organizations with requirements for engineering 3D workloads.
When you use AVD on its own (or natively), the only location you can run and manage your resources is in Azure. If you have resources on-prem and adopt AVD only, your users will have to access those resources in a different location (no central management or access location). But if you use Citrix on AVD, management of resources for both cloud and on-prem happens in a central management location.
In addition, you can provide users with a single point to log in and access all their resources. As we all know, most business today demands a hybrid environment, and this is constantly changing with the continued need to modernize, migrate, and adopt the cloud to scale.
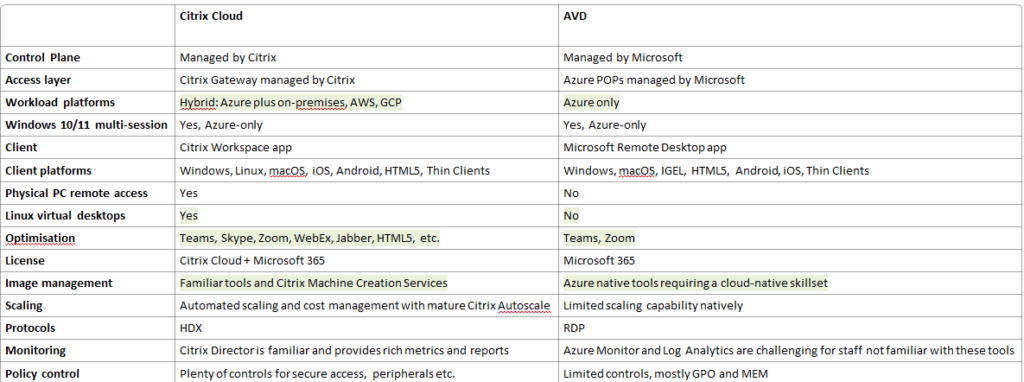
The combination of WVD and Citrix offers the following advantages:
- Optimization packs for Microsoft Teams and Skype for Business—provides a good audio-visual experience for Microsoft Teams and Skype for Business.
- Hybrid Cloud Model—WVD can only run Windows 10 workloads in multiple sessions on Azure. Citrix provides the ability to also run existing RDSH workloads, either on-premises, on Azure, on any other cloud, or on HCI solutions like Nutanix.
- Citrix HDX—an improved remoting protocol.
- Citrix Machine Creation Services (MCS)—provides a hypervisor API that enables quick generation of VMs with minimal infrastructure utilization.
- AutoScale—quickly adds or removes workloads as needed, with “vertical load balancing” which balances the number of user sessions on a single machine until optimal performance is reached, improving utilization and reducing the number of servers needed.
- App Layering—this Citrix capability significantly reduces management time for Windows images and applications. It separates the applications from the management infrastructure and the operating system. It lets you install each application and operating system patch only once, then update the appropriate template and reload the image.
- App Protection—this Citrix feature improves security when using public resources on virtual desktops and Citrix applications.
- Session Recording—lets users record screen activity during VDA-hosted user sessions for any connection type, in accordance with company policies.
- Citrix Analytics—security and performance analysis leveraging AI, which can help identify and resolve issues and anomalies.
- Citrix SD-WAN—Citrix SD-WAN is a next-generation WAN solution that provides better security, and an improved application environment for SaaS, cloud, virtual applications and desktops.
- Multi-factor authentication (MFA)—Citrix integrates with third-party MFA providers, including Okta, OAuth, and RADIUS.
References:
Tech Brief: Enhancing Azure Virtual Desktop | Citrix Tech Zone
(2) Citrix+Microsoft: Citrix DaaS on Azure Technical Webinar – YouTube