Azure AD Authentication for applications
Users may be required to authenticate to their applications (for example, Microsoft 365 apps, Teams (work or school), OneDrive, etc.) at every sign-in. The repeated authentication prompts are due to the virtual machines Azure AD device state. We recommend virtual machines are Azure AD Joined (AADJ) or Hybrid Azure AD Joined (HAADJ) for the best user experience.
Virtual machines, which are AADJ or HAADJ create the user’s primary refresh token (PRT) at sign-in. Primary refresh token(s) created at sign-in will be used to authenticate to Azure AD based applications. Standard Domain Joined (DJ) virtual machines don’t create a PRT at sign-in, instead rely on the Microsoft Azure AD broker plugin.
Azure AD broker directories and apps
Starting in FSLogix 2210 (2.9.8361.52326) and later versions, all content stored in following locations is no longer roamed as part of the user profile.
%USERPROFILE%\AppData\Local\Packages\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy%USERPROFILE%\AppData\Local\Packages\Microsoft.Windows.CloudExperienceHost_cw5n1h2txyewy%USERPROFILE%\AppData\Local\Microsoft\TokenBroker
Determining your device status
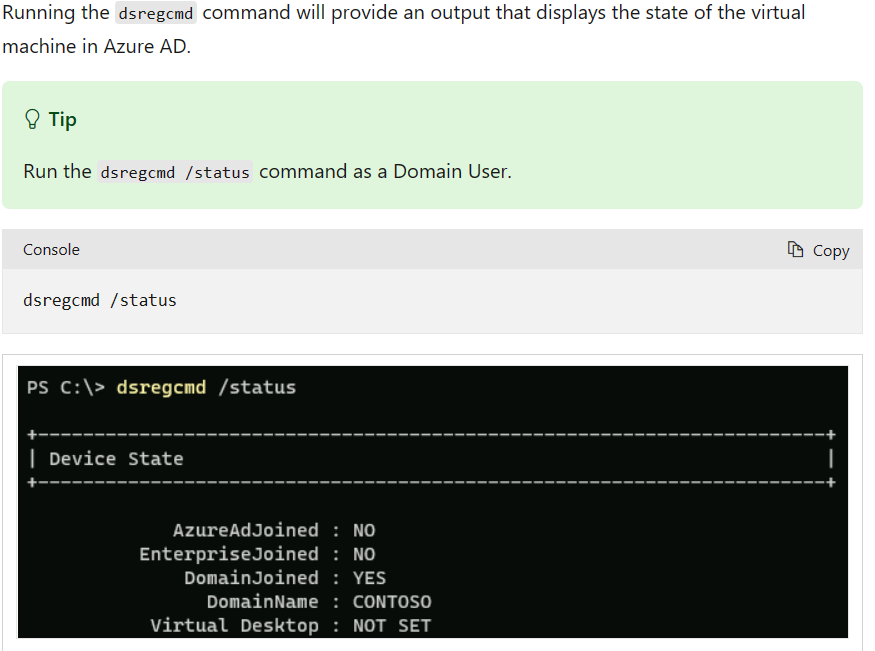
The following articles are provided to help determine whether or not your virtual machines are configured to use primary refresh tokens as part of an Azure AD sign-in process.
- Azure AD Integration Methods
- Device identity and desktop virtualization
- Troubleshoot devices by using the dsregcmd command
When using non-persistent VDI, you need to prevent users from adding work or school accounts. Use the below registry entry to prevent adding these virtual machines to your Azure AD directory. Failure to do so will result in your directory having lots of stale Hybrid Azure AD joined devices that were registered from your non-persistent VDI platform resulting in increased pressure on your tenant quota and risk of service interruption because of running out of tenant quota.
HKLM\SOFTWARE\Policies\Microsoft\Windows\WorkplaceJoin: "BlockAADWorkplaceJoin"=dword:00000001
Reference