Category: Azure (Page 1 of 3)
Azure AD Authentication for applications
Users may be required to authenticate to their applications (for example, Microsoft 365 apps, Teams (work or school), OneDrive, etc.) at every sign-in. The repeated authentication prompts are due to the virtual machines Azure AD device state. We recommend virtual machines are Azure AD Joined (AADJ) or Hybrid Azure AD Joined (HAADJ) for the best user experience.
Virtual machines, which are AADJ or HAADJ create the user’s primary refresh token (PRT) at sign-in. Primary refresh token(s) created at sign-in will be used to authenticate to Azure AD based applications. Standard Domain Joined (DJ) virtual machines don’t create a PRT at sign-in, instead rely on the Microsoft Azure AD broker plugin.
Azure AD broker directories and apps
Starting in FSLogix 2210 (2.9.8361.52326) and later versions, all content stored in following locations is no longer roamed as part of the user profile.
%USERPROFILE%\AppData\Local\Packages\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy%USERPROFILE%\AppData\Local\Packages\Microsoft.Windows.CloudExperienceHost_cw5n1h2txyewy%USERPROFILE%\AppData\Local\Microsoft\TokenBroker
Determining your device status
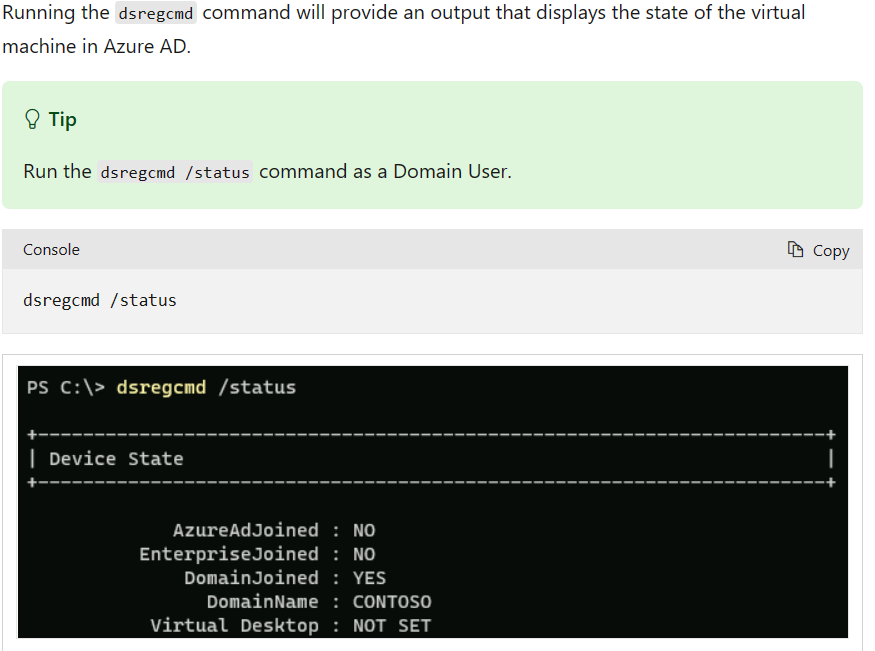
The following articles are provided to help determine whether or not your virtual machines are configured to use primary refresh tokens as part of an Azure AD sign-in process.
- Azure AD Integration Methods
- Device identity and desktop virtualization
- Troubleshoot devices by using the dsregcmd command
When using non-persistent VDI, you need to prevent users from adding work or school accounts. Use the below registry entry to prevent adding these virtual machines to your Azure AD directory. Failure to do so will result in your directory having lots of stale Hybrid Azure AD joined devices that were registered from your non-persistent VDI platform resulting in increased pressure on your tenant quota and risk of service interruption because of running out of tenant quota.
HKLM\SOFTWARE\Policies\Microsoft\Windows\WorkplaceJoin: "BlockAADWorkplaceJoin"=dword:00000001
Reference
Below script used to assign NTFS permissions( List,Read,Traverse, Create/Append) for FSlogix user profiles, it provides users not to access other folders
#Below script used to assign NTFS permissions( List,Read,Traverse, Create/Append) for FSlogix user profiles, it provides users not to access other folders
# User Groups/Users are given in input file , Keep Heading(top) GROUPS and provide groupnames under that
# Input your Storage account name and Domain Name in below script
# Whoever runs the below code, he should have full admin privilege
$permission = ":(X,RD,AD,RC)"
$Lists = Import-csv -Path "C:\temp\devgroups.csv" #group Accounts
$shares = "<Share Name 1>,<Share Name 2>"
$sharelist = $shares.Split(",")
foreach($share in $sharelist)
{
$share
$shrpath=\\<storageAccountName>.file.core.windows.net\$share
foreach($list in $lists)
{
$UserName = $list.groups
Invoke-Expression -Command ('icacls $shrpath /grant "<Domain Name>\${UserName}${permission}"')
}
}
We had a requirement to migrated 8000+ Citrix User UPM profiles across globe to FSLogix Profiles (.VHDX) as customer wanted to move from Citrix to AVD. This was a very challenging requirement due to new experience
#Below Script used to convert UPM Profile Path to FSlogix profile path by retaining NTFS Permissions
# Fslogix Root profile path
$newprofilepath = "\\<StorageAccountName>.file.core.windows.net\<ShareName>"
# UPM Root profile path
$oldprofilepath = "<Profile Share Path>" # Provide UPM Profile Path
$newusers = @()
ForEach ($user in(gc "C:\temp\users.txt")) {
$path = $oldprofilepath + $user
if(Test-Path -Path $path){
$newusers += $user
}
else{
Write-Output "$user does not exist"
}
}
ForEach ($user in $newusers) {
# Subfolder 1 - First Path to UPM_Profile Folder in UPM Profiles
$subfolder1 = ""
# Subfolder 2 - First Path to UPM_Profile Folder in UPM Profiles
#$subfolder2 =
$sam = "$user"
Start-Sleep -s 10
######################################################
$iniownr = (Get-Acl (Get-ChildItem "C:\temp\$sam" -force -Recurse ).FullName).Owner
takeown /f $sam /r /d y
Start-Sleep -s 10
icacls "C:\Temp\$sam" /grant zs_wvd_prod:f /q /c /t
#####################################################
Start-Sleep -s 10
#########################################################################################
# Do not edit here
#########################################################################################
$old = $oldprofilepath + $sam + $subfolder1;
$sid = (New-Object System.Security.Principal.NTAccount($sam)).translate([System.Security.Principal.SecurityIdentifier]).Value
$regtext = "Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\$sid]
`"ProfileImagePath`"=`"C:\\Users\\$sam`"
`"FSL_OriginalProfileImagePath`"=`"C:\\Users\\$sam`"
`"Flags`"=dword:00000000
`"State`"=dword:00000000
`"ProfileLoadTimeLow`"=dword:00000000
`"ProfileLoadTimeHigh`"=dword:00000000
`"RefCount`"=dword:00000000
`"RunLogonScriptSync`"=dword:00000000
"
$nfolder = join-path $newprofilepath ($sid+"_"+$sam)
if (!(test-path $nfolder)) {New-Item -Path $nfolder -ItemType directory | Out-Null}
#& icacls $nfolder /setowner "$env:userdomain\$sam" /T /C
#& icacls $nfolder /grant $env:userdomain\$sam`:`(OI`)`(CI`)F /T
& icacls $nfolder /grant $sam`:`(OI`)`(CI`)F /T
$vhd = Join-Path $nfolder ("Profile_"+$sam+".vhdx")
$script1 = "create vdisk file=`"$vhd`" maximum 30720 type=expandable"
$script2 = "sel vdisk file=`"$vhd`"`r`nattach vdisk"
$script3 = "sel vdisk file=`"$vhd`"`r`ncreate part prim`r`nselect part 1`r`nformat fs=ntfs quick"
$script4 = "sel vdisk file=`"$vhd`"`r`nsel part 1`r`nassign letter=T"
$script5 = "sel vdisk file`"$vhd`"`r`ndetach vdisk"
$script6 = "sel vdisk file=`"$vhd`"`r`nattach vdisk readonly`"`r`ncompact vdisk"
if (!(test-path $vhd)) {
$script1 | diskpart
$script2 | diskpart
Start-Sleep -s 5
$script3 | diskpart
$script4 | diskpart
& label T: Profile-$sam
New-Item -Path T:\Profile -ItemType directory | Out-Null
start-process icacls "T:\Profile /setowner SYSTEM"
Start-Process icacls -ArgumentList "T:\Profile /inheritance:r"
$cmd1 = "T:\Profile /grant $env:userdomain\$sam`:`(OI`)`(CI`)F"
Start-Process icacls -ArgumentList "T:\Profile /grant SYSTEM`:`(OI`)`(CI`)F"
Start-Process icacls -ArgumentList "T:\Profile /grant Administrators`:`(OI`)`(CI`)F"
Start-Process icacls -ArgumentList $cmd1
} else {
$script2 | diskpart
Start-Sleep -s 5
$script4 | diskpart
}
"Copying $old to $vhd"
& robocopy $old T:\Profile /MIR /r:0 | Out-Null
if (!(Test-Path "T:\Profile\AppData\Local\FSLogix")) {
New-Item -Path "T:\Profile\AppData\Local\FSLogix" -ItemType directory | Out-Null
}
if (!(Test-Path "T:\Profile\AppData\Local\FSLogix\ProfileData.reg")) {$regtext | Out-File "T:\Profile\AppData\Local\FSLogix\ProfileData.reg" -Encoding ascii}
$script5 | diskpart
############################################################
Start-Sleep -s 10
icacls "C:\Temp\$sam" /grant $iniownr:f /q /c /t
}What is Azure Files?
Azure Files offers fully managed file shares in the cloud that are accessible via the industry standard Server Message Block (SMB) protocol or Network File System (NFS) protocol. Azure Files file shares can be mounted concurrently by cloud or on-premises deployments. SMB Azure file shares are accessible from Windows, Linux, and macOS clients. NFS Azure Files shares are accessible from Linux or macOS clients. Additionally, SMB Azure file shares can be cached on Windows Servers with Azure File Sync for fast access near where the data is being used
Why would I use an Azure file share versus Azure Blob storage for my data?
Azure Files and Azure Blob storage both offer ways to store large amounts of data in the cloud, but they are useful for slightly different purposes.
Azure Blob storage is useful for massive-scale, cloud-native applications that need to store unstructured data. To maximize performance and scale, Azure Blob storage is a simpler storage abstraction than a true file system. You can access Azure Blob storage only through REST-based client libraries (or directly through the REST-based protocol).
Azure Files is specifically a file system. Azure Files has all the file abstracts that you know and love from years of working with on-premises operating systems. Like Azure Blob storage, Azure Files offers a REST interface and REST-based client libraries. Unlike Azure Blob storage, Azure Files offers SMB or NFS access to Azure file shares. File shares can be mounted directly on Windows, Linux, or macOS, either on-premises or in cloud VMs, without writing any code or attaching any special drivers to the file system. You also can cache Azure SMB file shares on on-premises file servers by using Azure File Sync for quick access, close to where the data is used.
For a more in-depth description on the differences between Azure Files and Azure Blob storage, see Introduction to the core Azure Storage services. To learn more about Azure Blob storage, see Introduction to Blob storage.
Azure Files Connectivity options
We have some different connectivity options available to us depending on whether we’re accessing our file shares either internally or externally. In this context, accessing it internally or externally implies the Azure region where our storage account exists, where the file share exists.
• Internal connectivity: This implies that the clients accessing the file share are within the Azure cloud itself. Here we have the ability to use REST, SMB 2.1 and SMB 3.0.
• External connectivity: In this scenario, the client machines accessing the file shares are located in a different cloud environment or could also reside on premises. We only have the option of using REST and SMB 3.0 in this case because SMB 2.1 doesn’t provide the encryption which is required for connecting externally to ensure the safety of the data.
In terms of security, data encrypted at rest by default within our storage accounts and we have access to secure data transfer over HTTPS for data that is in transit. This allows us to protect our data, whether it’s at rest or in transit inside of our Azure Files.
Creating an Azure File Share
Prerequisites
- Create a storage account
- Traditional AD environment synchronized to Azure AD with Azure AD Connect
- Account credentials to perform the steps below to create a computer account in an existing Active Directory environment to connect with Azure Files.
- Permissions to create the storage account
Before you can work with an Azure file share, you have to create an Azure storage account. A general-purpose v2 storage account provides access to all of the Azure Storage services: blobs, files, queues, and tables.
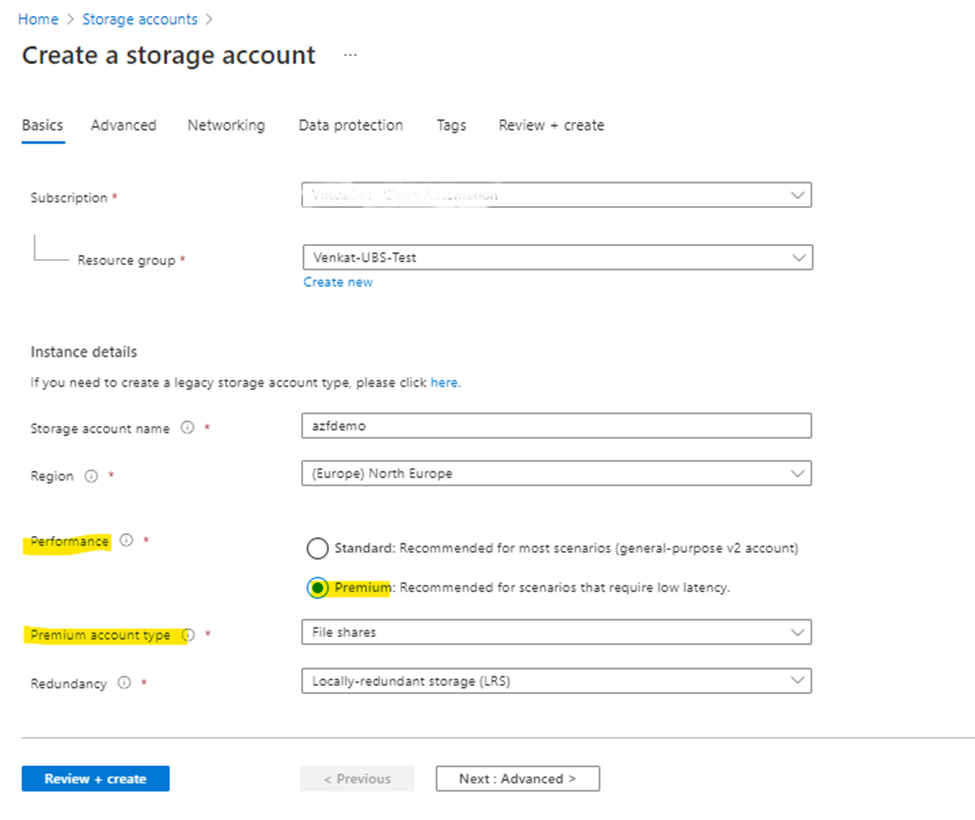
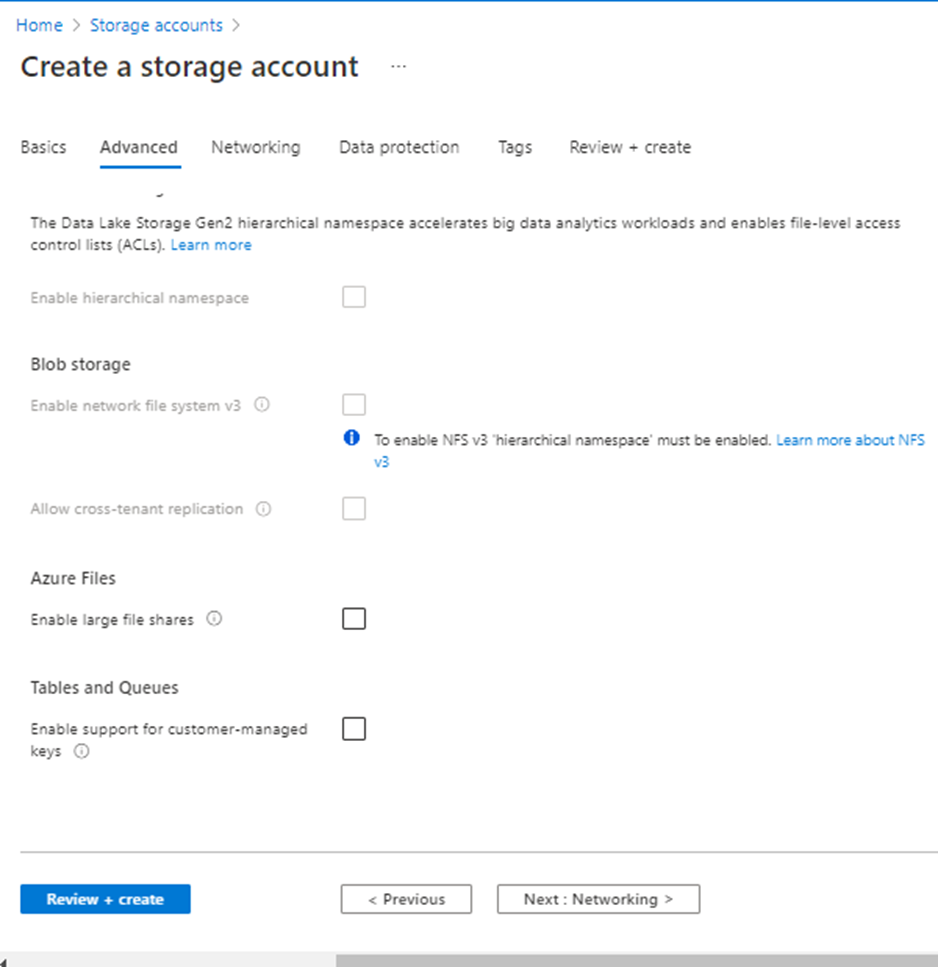
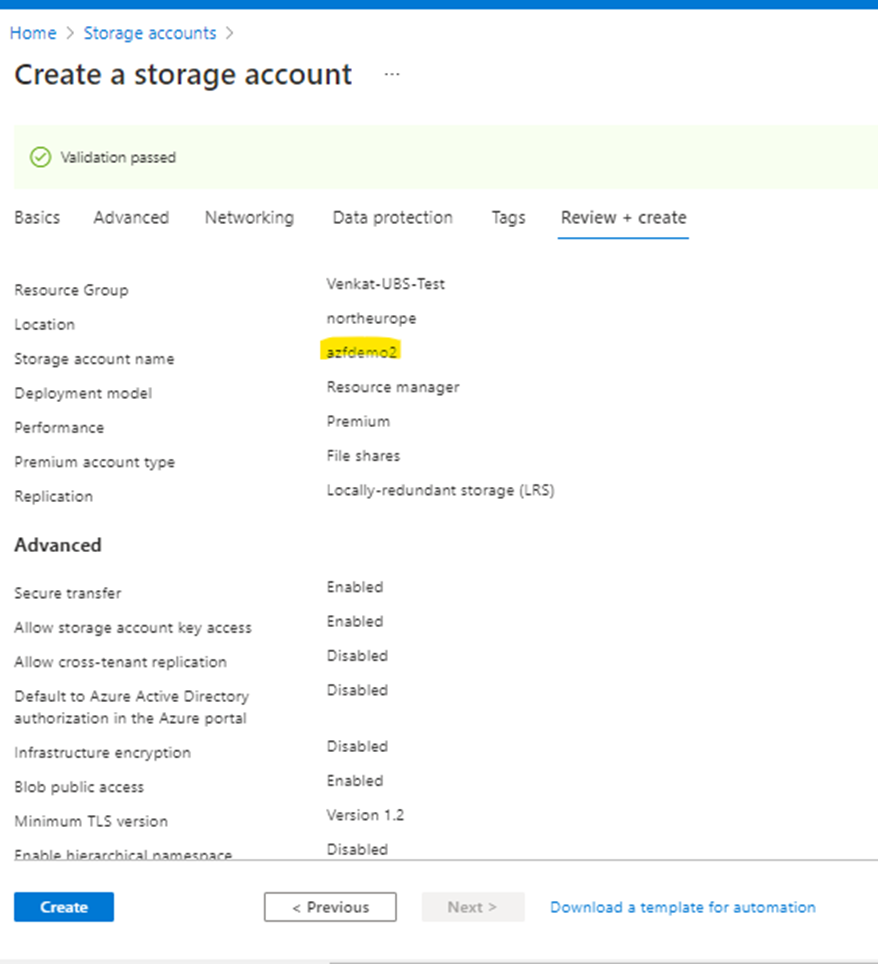
As I have a requirement for Premium, below screenshots are provided with Premium Type and note that options may vary based on selection of storage account type.
Storage Accounts ->Create New
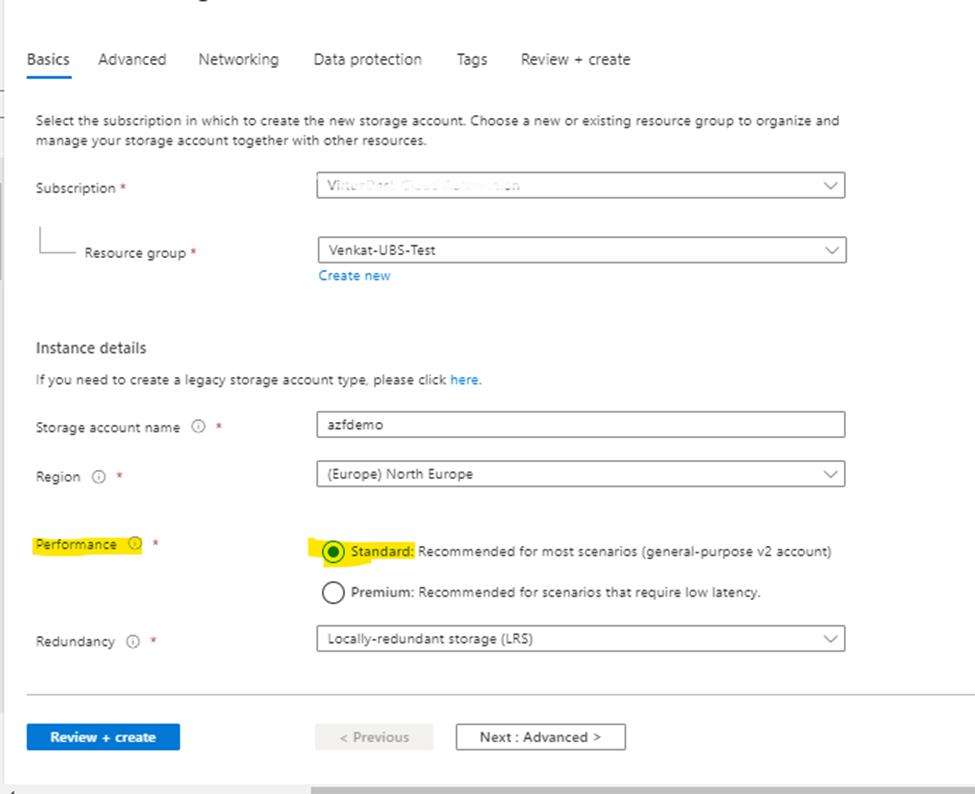
In above screenshot, I selected Performance Type as “Standard”. In case, if you have a requirement for Premium file Type then options will be displayed as below
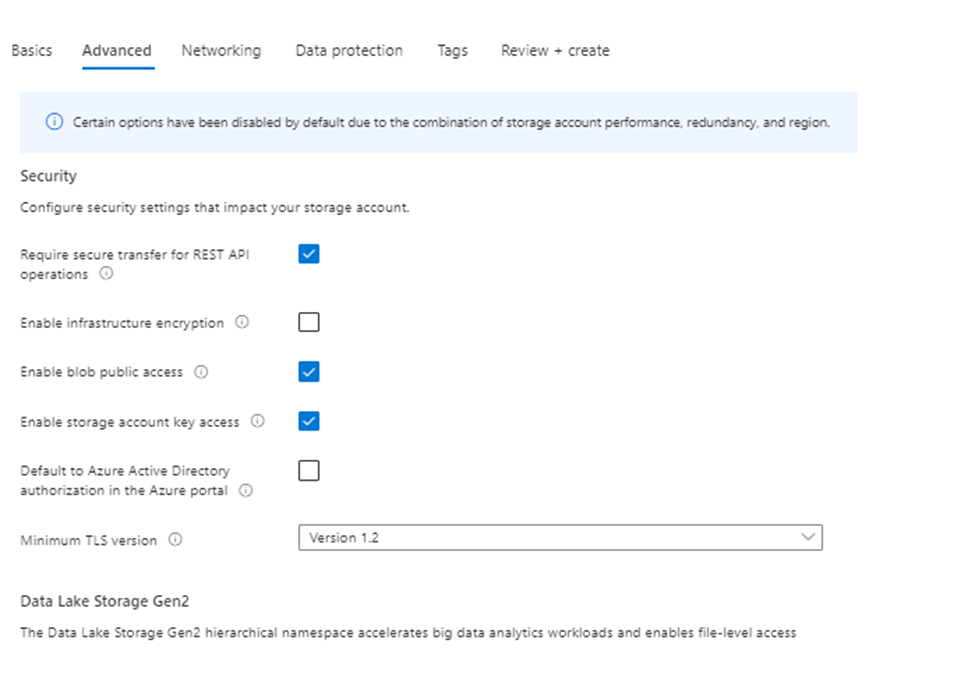
Click Next (Default options)
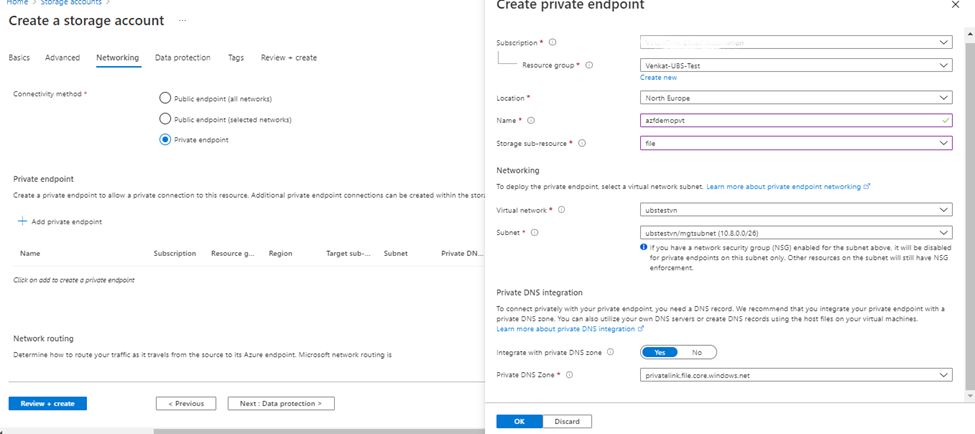
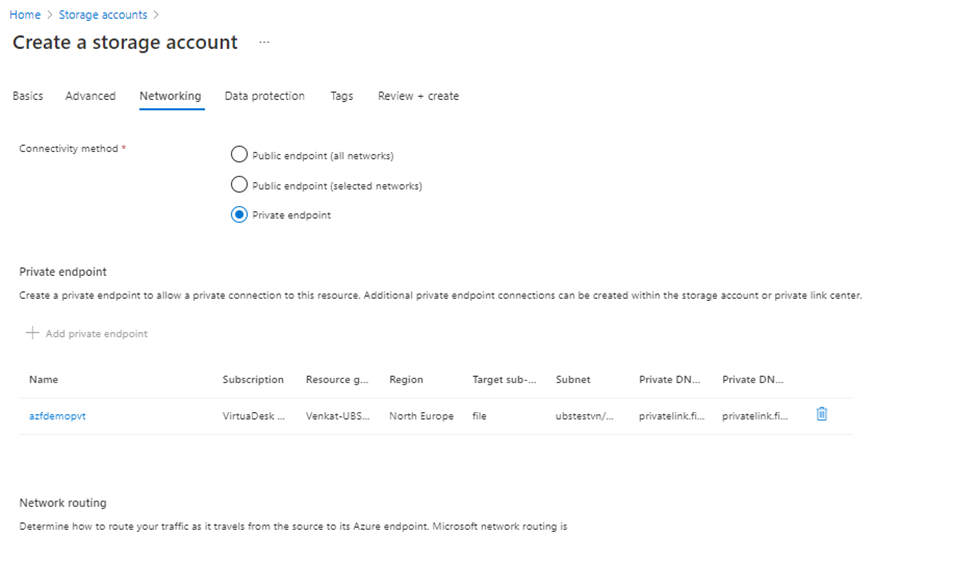
Under Networking ->Create Private Endpoint (best practice)
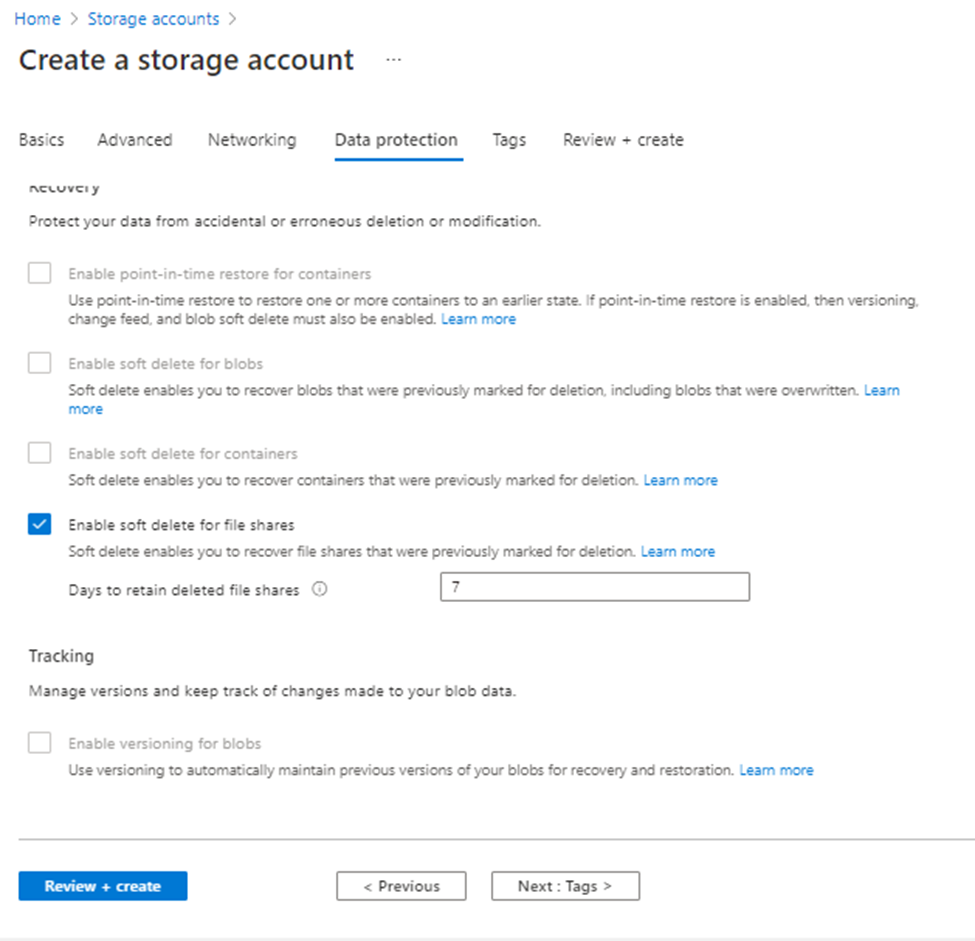
Click Next (Default Options)
Click Next and validate to create
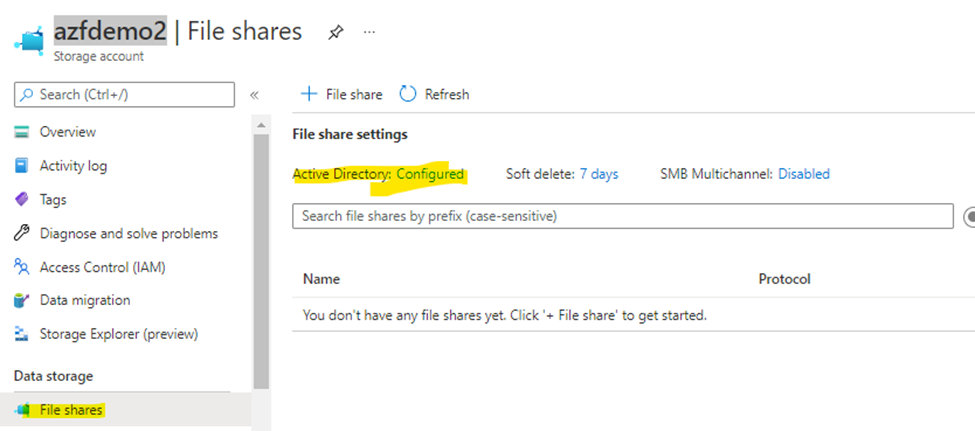
Enable AD DS authentication & Authorization for your Azure file shares -> Onpremises AD DS Authentication
Azure Files supports identity-based authentication over Server Message Block (SMB) through two types of Domain Services: on-premises Active Directory Domain Services (AD DS) and Azure Active Directory Domain Services (Azure AD DS). We strongly recommend you to review the How it works section to select the right domain service for authentication. The setup is different depending on the domain service you choose.
Supported scenarios and restrictions
• AD DS Identities used for Azure Files on-premises AD DS authentication must be synced to Azure AD. Password hash synchronization is optional.
• Supports Azure file shares managed by Azure File Sync.
• Supports Kerberos authentication with AD with RC4-HMAC and AES 256 encryption. AES 256 encryption support is currently limited to storage accounts with names <= 15 characters in length. AES 128 Kerberos encryption is not yet supported.
• Supports single sign-on experience.
• Only supported on clients running on OS versions newer than Windows 7 or Windows Server 2008 R2.
• Only supported against the AD forest that the storage account is registered to. You can only access Azure file shares with the AD DS credentials from a single forest by default. If you need to access your Azure file share from a different forest, make sure that you have the proper forest trust configured, see the FAQ for details.
• Does not support authentication against computer accounts created in AD DS.
• Does not support authentication against Network File System (NFS) file shares.
When you enable AD DS for Azure file shares over SMB, your AD DS-joined machines can mount Azure file shares using your existing AD DS credentials. This capability can be enabled with an AD DS environment hosted either in on-prem machines or hosted in Azure.
Prerequisites
Before you enable AD DS authentication for Azure file shares, make sure you have completed the following prerequisites:
• Select or create your AD DS environment and sync it to Azure AD with Azure AD Connect.
You can enable the feature on a new or existing on-premises AD DS environment. Identities used for access must be synced to Azure AD. The Azure AD tenant and the file share that you are accessing must be associated with the same subscription.
• Domain-join an on-premises machine or an Azure VM to on-premises AD DS. For information about how to domain-join, refer to Join a Computer to a Domain.
Part one: Enable AD DS authentication for your Azure file shares
Option 1 (recommended): Use AzFilesHybrid PowerShell module
1.1.1 Download AzFilesHybrid module
• If you don’t have .NET Framework 4.7.2 installed, install it now. It is required for the module to import successfully.
• Download and unzip the AzFilesHybrid module (GA module: v0.2.0+) Note that AES 256 kerberos encryption is supported on v0.2.2 or above. If you have enabled the feature with a AzFilesHybrid version below v0.2.2 and want to update to support AES 256 Kerberos encryption, please refer to this article.
• Install and execute the module in a device that is domain joined to on-premises AD DS with AD DS credentials that have permissions to create a service logon account or a computer account in the target AD.
• Run the script using an on-premises AD DS credential that is synced to your Azure AD. The on-premises AD DS credential must have either Owner or Contributor Azure role on the storage account.
Ref: Enable AD DS authentication to Azure file shares | Microsoft Docs
1.1.2 Run Join-AzStorageAccountForAuth
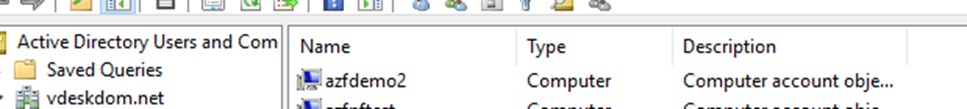
The Join-AzStorageAccountForAuth cmdlet performs the equivalent of an offline domain join on behalf of the specified storage account. The script uses the cmdlet to create a computer account in your AD domain. If for whatever reason you cannot use a computer account, you can alter the script to create a service logon account instead. If you choose to run the command manually, you should select the account best suited for your environment.
The AD DS account created by the cmdlet represents the storage account. If the AD DS account is created under an organizational unit (OU) that enforces password expiration, you must update the password before the maximum password age. Failing to update the account password before that date results in authentication failures when accessing Azure file shares. To learn how to update the password,
Execute below are the steps if Azure Powershell & Azure storage modules not available at client system where you are trying to execute the Join-AzStorageAccountForAuth PowerShell commands
Install-Module Az.Accounts
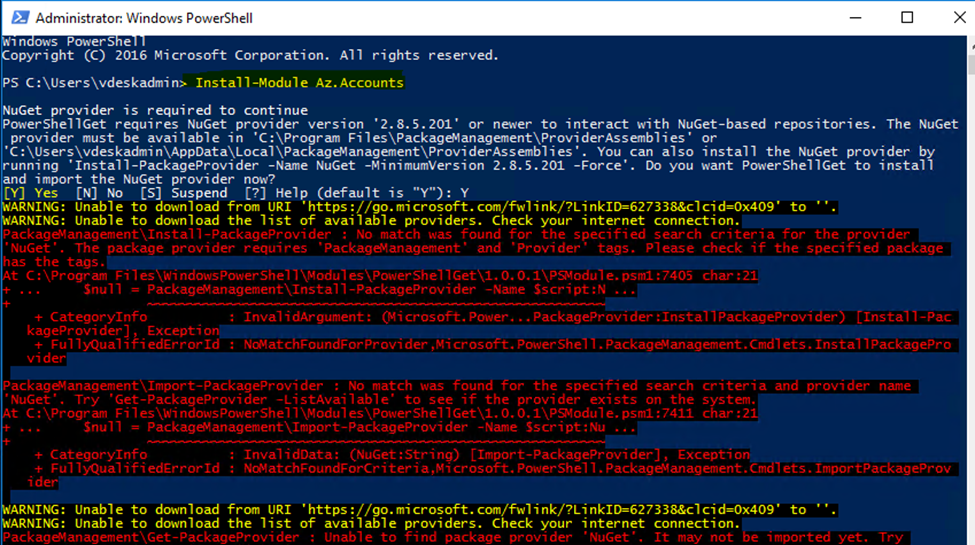
The problem is that we are unable to install NuGet provider and a couple of errors are showing. Warning unable to download from URI, unable to download the list of available providers. After the errors, it did not install. In this article, you will learn why this is happening and the solution for installing NuGet provider for PowerShell.,
Follow below steps to resolve the above error
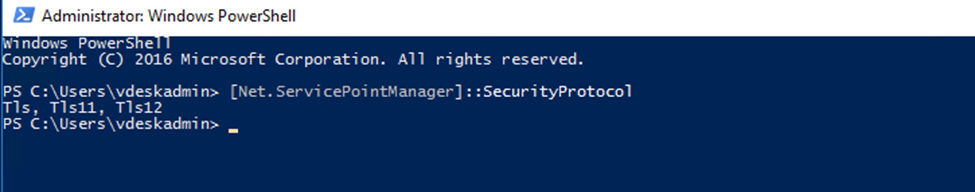
First, check the SSL version with below command
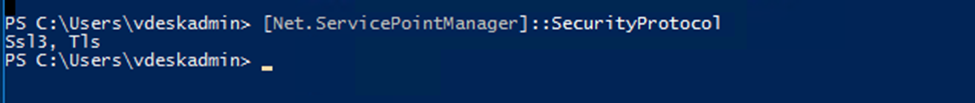
Solution for unable to install NuGet provider for PowerShell
Now that we gathered all the information, we are going to enable TLS 1.2 on the system. Run both cmdlets to set .NET Framework strong cryptography registry keys. After that, restart PowerShell and check if the security protocol TLS 1.2 is added
The first cmdlet is to set strong cryptography on 64 bit .Net Framework (version 4 and above).
Set-ItemProperty -Path ‘HKLM:\SOFTWARE\Wow6432Node\Microsoft.NetFramework\v4.0.30319’ -Name ‘SchUseStrongCrypto’ -Value ‘1’ -Type Dword
The second cmdlet is to set strong cryptography on 32 bit .Net Framework (version 4 and above).
Set-ItemProperty -Path ‘HKLM:\SOFTWARE\Microsoft.NetFramework\v4.0.30319’ -Name ‘SchUseStrongCrypto’ -Value ‘1’ -Type Dword
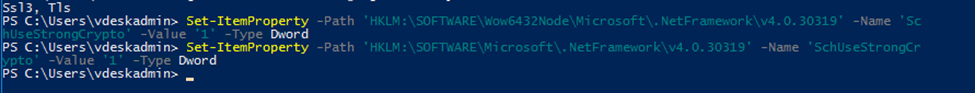
Restart Powershell and check for supported security protocols.
Run again Install-Module Az.Accounts
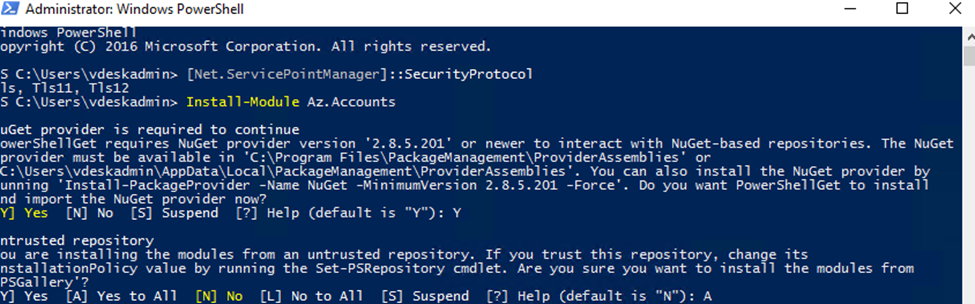
Post installation, Import Modules ( Installed Modules can be seen in C:\Program Files\WindowsPowerShell\Modules)
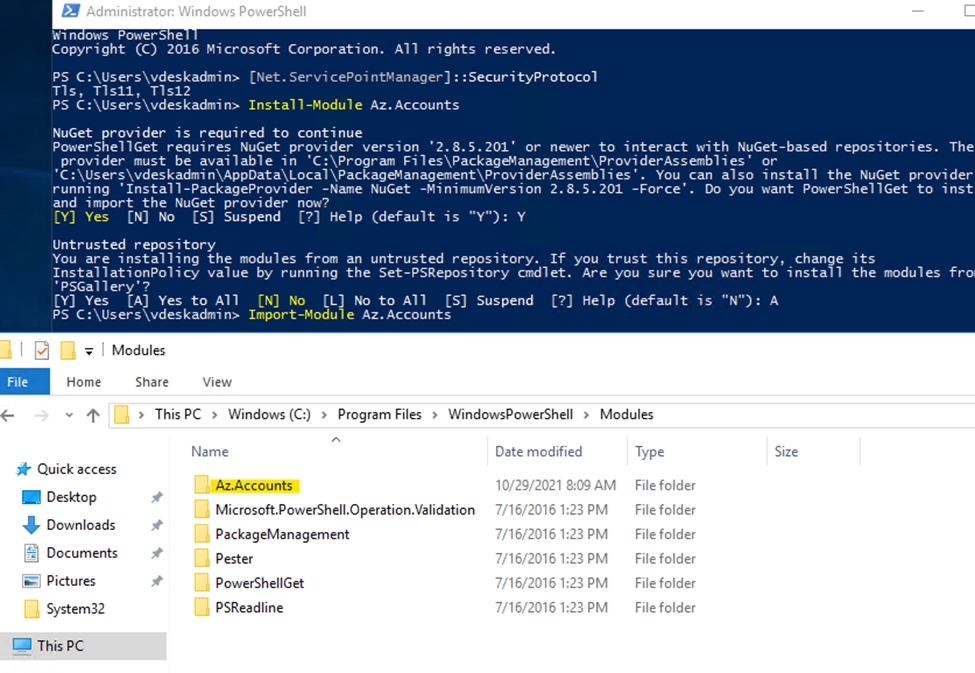
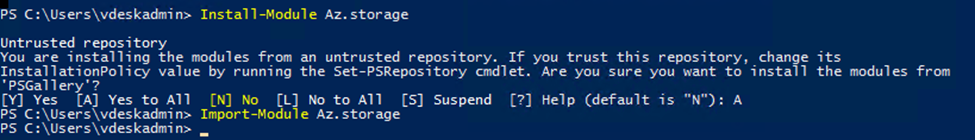
Similarly do for Azure storage modules
Now Install, Azure Hybrid Modules by following KB Enable AD DS authentication to Azure file shares | Microsoft Docs
Steps:
.\CopyToPSPath.ps1
Connect-AzAccount
(Note: connect the Azure with required credentials ( i.e, account should have permission to access storage and create computer account in domain)
Import-Module AzFilesHybrid
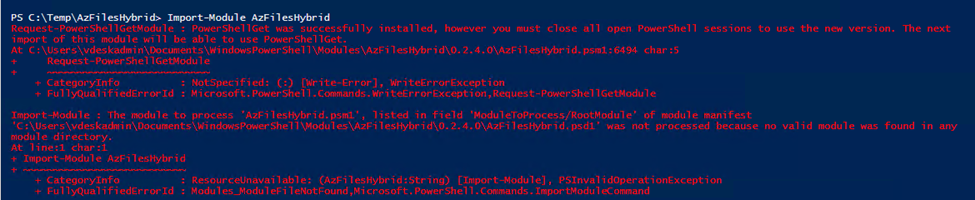
For above warning, close powershell and reopen
Join-AzStorageAccountForAuth -ResourceGroupName $ResourceGroupName
-StorageAccountName $StorageAccountName -DomainAccountType $DomainAccountType
-OrganizationalUnitDistinguishedName $OuDistinguishedName `
Note: Add OrganizationalUnitDistinguishedName if computer account need to join in specific OU
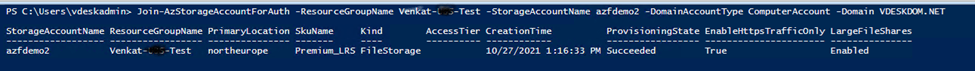
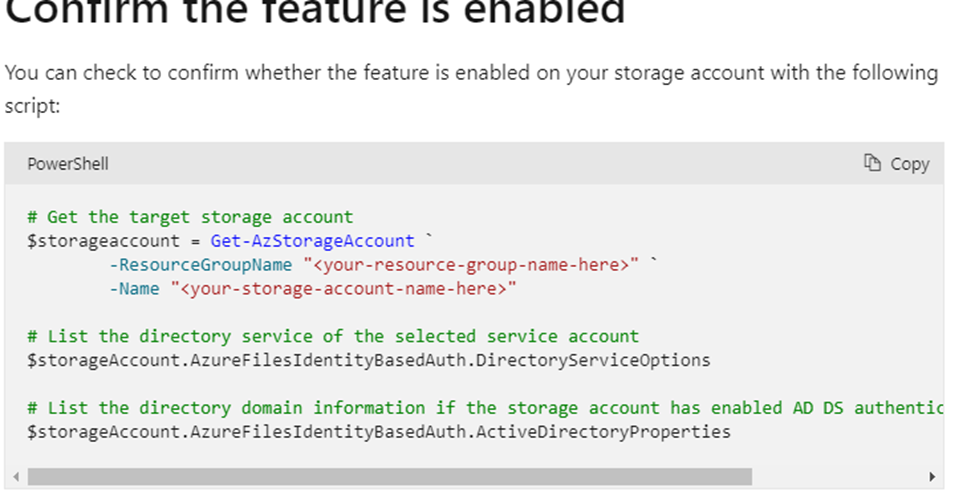
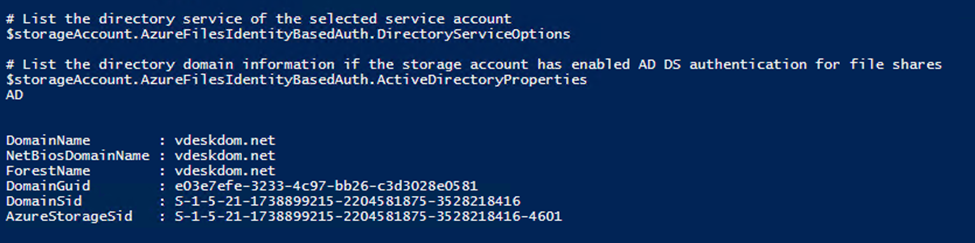
Post execution ->verify from below tools
Or through PowerShell
Note:
Update the password of your storage account identity in AD DS
If you registered the Active Directory Domain Services (AD DS) identity/account that represents your storage account in an organizational unit or domain that enforces password expiration time, you must change the password before the maximum password age. Your organization may run automated cleanup scripts that delete accounts once their password expires. Because of this, if you do not change your password before it expires, your account could be deleted, which will cause you to lose access to your Azure file shares.
To trigger password rotation, you can run the Update-
AzStorageAccountADObjectPassword command from the AzFilesHybrid module
Ref: Update AD DS storage account password | Microsoft Docs
Part 2: Assign share-level permissions to an identity
Once you’ve enabled Active Directory Domain Services (AD DS) authentication on your storage account, you must configure share-level permissions in order to get access to your file shares. There are two ways you can assign share-level permissions. You can assign them to specific Azure AD users/user groups and you can assign them to all authenticated identities as a default share level permission.
Share-level permissions for specific Azure AD users or groups
Share-level permissions must be assigned to the Azure AD identity representing the same user or group in your AD DS to support AD DS authentication to your Azure file share. Authentication and authorization against identities that only exist in Azure AD, such as Azure Managed Identities (MSIs), are not supported with AD DS authentication.
You can use the Azure portal, Azure PowerShell module, or Azure CLI to assign the built-in roles to the Azure AD identity of a user for granting share-level permissions.
Note: The share level permissions will take upto 3 hours to take effect once completed. Please wait for the permissions to sync before connecting to your file share using your credentials
Share-level permissions for all authenticated identities
You can add a default share-level permission on your storage account, instead of configuring share-level permissions for Azure AD users or groups. A default share-level permission assigned to your storage account applies to all file shares contained in the storage account.
When you set a default share-level permission, all authenticated users and groups will have the same permission. Authenticated users or groups are identified as the identity can be authenticated against the on-premises AD DS the storage account is associated with. The default share level permission is set to None at initialization, implying that no access is allowed to files & directories in Azure file share.
Note: You cannot currently assign permissions to the storage account with the Azure portal. Use either the Azure PowerShell module or the Azure CLI, instead.
Ref: Control access to Azure file shares – on-premises AD DS authentication | Microsoft Docs
Mount a file share from a domain-joined VM
Mounting prerequisites
Before you can mount the file share, make sure you’ve gone through the following pre-requisites:
• If you are mounting the file share from a client that has previously mounted the file share using your storage account key, make sure that you have disconnected the share, removed the persistent credentials of the storage account key, and are currently using AD DS credentials for authentication. For instructions to clear the mounted share with storage account key, refer to FAQ page.
• Your client must have line of sight to your AD DS. If your machine or VM is out of the network managed by your AD DS, you will need to enable VPN to reach AD DS for authentication.
Replace the placeholder values with your own values, then use the following command to mount the Azure file share. You always need to mount using the path shown below. Using CNAME for file mount is not supported for identity based authentication (AD DS or Azure AD DS).
Ref: Mount Azure file share to an AD DS-joined VM | Microsoft Docs
Enable Azure Active Directory Domain Services authentication on Azure Files
Ref:Use Azure AD Domain Services to authorize access to file data over SMB | Microsoft Docs
Extracted from MS Tech community
While volume activation is a process that many have utilized over the years, today’s post offers guidance to help you ensure that all your devices have been properly activated regardless of their connection to your organization’s network.
First, a refresher. Volume activation enables a wide range of Windows devices to receive a volume license and be activated automatically and en masse versus tediously entering an activation key on each Windows device manually.
The most common methods of volume activation require that devices to be connected to an organization’s network or connected via virtual private network (VPN) to “check in” from time to time with the organization’s activation service to maintain their licenses. When people work from home and off the corporate or school network; however, their devices’ ability to receive or maintain activation is limited.
Volume activation methods
There are several methods to activate devices via volume licensing. For detailed information, see Plan for volume activation. Here, however, is a summary for easy reference.
Key Management Service
Key Management Service (KMS) activation requires TCP/IP connectivity to, and accessibility from, an organization’s private network so that licenses are not accessible to anyone outside of the organization. By default, KMS hosts and clients use DNS to publish and find the KMS key. Default settings can be used, which require little or no administrative action, or KMS hosts and client computers can be manually configured based on network configuration and security requirements.
KMS activations are valid for 180 days (the activation validity interval). KMS client computers must renew their activation by connecting to the KMS host at least once every 180 days. By default, KMS client computers attempt to renew their activation every 7 days. If KMS activation fails, the client computer retries to reach the host every two hours. After a client computer’s activation is renewed, the activation validity interval begins again.
Multiple Activation Key
A Multiple Activation Key (MAK) is used for one-time activation with Microsoft’s hosted activation services. Each MAK has a predetermined number of activations allowed. This number is based on volume licensing agreements, and it might not match the organization’s exact license count. Each activation that uses a MAK with the Microsoft-hosted activation service counts toward the activation limit.
You can use a MAK for individual computers or with an image that can be duplicated or installed using Microsoft deployment solutions. You can also use a MAK on a computer that was originally configured to use KMS activation, which is useful for moving a computer off the core network to a disconnected environment.
Active Directory-based activation
Active Directory-based activation is similar to KMS activation but uses Active Directory instead of a separate service. Active Directory-based activation is implemented as a role service that relies on Active Directory Domain Services to store activation objects. Active Directory-based activation requires that the forest schema be updated using adprep.exe on a supported server operating system, but after the schema is updated, older domain controllers can still activate clients.
Devices activated via Active Directory maintain their activated state for up to 180 days after the last contact with the domain. Devices periodically attempt to reactivate (every seven days by default) before the end of that period and, again, at the end of the 180 days.
Windows 10 Subscription Activation
Starting with Windows 10, version 1703 Windows 10 Pro supports the Subscription Activation feature, enabling users to “step-up” from Windows 10 Pro to Windows 10 Enterprise automatically if they are subscribed to Windows 10 Enterprise E3 or E5.
With Windows 10, version 1903 the Subscription Activation feature also supports the ability to step-up from Windows 10 Pro Education to the Enterprise grade edition for educational institutions – Windows 10 Education.
The Subscription Activation feature eliminates the need to manually deploy Windows 10 Enterprise or Education images on each target device, then later standing up on-prem key management services such as KMS or MAK based activation, entering GVLKs, and subsequently rebooting client devices.
To step a device up to Windows 10 Education via Subscription Activation the device must meet the following requirements:
- Windows 10 Pro Education, version 1903 or later installed on the devices to be upgraded.
- A device with a Windows 10 Pro Education digital license. You can confirm this information in Settings > Update & Security > Activation.
- The Education tenant must have an active subscription to Microsoft 365 with a Windows 10 Enterprise license or a Windows 10 Enterprise or Education subscription.
- Devices must be Azure AD-joined or Hybrid Azure AD joined. Workgroup-joined or Azure AD registered devices are not supported.
| Note: If Windows 10 Pro is converted to Windows 10 Pro Education using benefits available in Store for Education, then the feature will not work. You will need to re-image the device using a Windows 10 Pro Education edition. |
Volume activation while working from home
If you activate devices in your organization using MAK, the activation process is straightforward and the devices are permanently activated. If you are using KMS or Active Directory-based Activation, each device must connect to the organization’s local network at least once every 180 days to “check in” with either the KMS host or the Active Directory domain controller. Otherwise, the user will be warned to activate Windows again.
With many users working or taking classes from home, a connection to the organization’s network may not exist, which would ultimately leave their devices in a deactivated state. There are a few options to avoid this:
- Use a VPN. By having the device connect to your organization’s network via a VPN, it will be able to contact a KMS host or Active Directory domain controller and will be able to maintain its activation status. If you manage your devices through a wholly on-premises solution to deploy policies, collect inventory, and deploy updates and other software, there is a good chance you are already using a VPN. Depending on the VPN configuration, some manual configuration of the client device may be required to ensure the KMS service is accessible through the VPN. For more details on these settings, which can be implemented via script, see Slmgr.vbs options for obtaining volume activation information.
- Convert the devices from KMS to MAK activation. By converting from KMS to MAK activation, you replace the license that requires reactivation every 180 days with a permanent one, which requires no additional check-in process. There are some cases—in educational organizations, for example—where each device is re-imaged at the end of the school year to get ready for the next class. In this case, the license must be “reclaimed” by contacting your Microsoft licensing rep or a Microsoft Licensing Activation Center.
One way of converting a device from KMS to MAK activation is to use the Windows Configuration Designer app (available from the Microsoft Store) to create a provisioning package, which includes the MAK, and deploy the package through email or a management solution such as Microsoft Intune.
You can also deploy a MAK directly within Intune without creating a provisioning package by creating a simple PowerShell script with the following commands and deploying the script to a user group:slmgr.vbs /ipk XXXXX-XXXXX-XXXXX-XXXXX-XXXXX slmgr.vbs /ato
(In the example above, XXXXX-XXXXX-XXXXX-XXXXX-XXXXX is your MAK key.)
It is important to monitor the success of these activations and remove users from the target group once their devices have been activated so that their other devices do not receive a new license.
Note: Windows Configuration Designer is also available as part of the Windows Assessment and Deployment Kit (ADK) for Windows 10. - Use Subscription Activation. This requires the devices to be joined to your Azure AD domain, enabling activation in the cloud. This is possible if you have one of the following subscriptions:
- Windows 10 Enterprise E3/E5
- Windows 10 Education A3/A5
- Windows 10 Enterprise with Software Assurance
- Microsoft 365 E3/E5
- Microsoft 365 E3/A5
- Microsoft 365 F1/F3
- Microsoft 365 Business Premium
If you need assistance and have one of the preceding subscriptions with at least 150 licenses, you may be eligible for assistance through FastTrack. Contact your Microsoft representative or request assistance from FastTrack and a Microsoft FastTrack representative will contact you directly.
Conclusion
Windows volume activation has been around for a long time, but the increased number of users working from home may require your organization to re-evaluate how to best keep your devices activated if they cannot reach your on-premises activation service if you are using KMS or Active Directory-based Activation. It is important to consider the options available to you to ensure your devices stay activated. As always, there is no “one-size-fits-all” approach, so consider the pros and cons of each option as you plan on how to best support your remote workers and students.
To learn more about activation, check Activate clients running Windows 10.
Below are the common WVD build issues which I encountered during implementations
Issue 1 -Unable to create any Host Pool
Error
{“code”:”DeploymentFailed”,”message”:”At least one resource deployment operation failed. Please list deployment operations for details. Please see https://aka.ms/DeployOperations for usage details.”,”details”:[{“code”:”Conflict”,”message”:”{\r\n \”status\”: \”Failed\”,\r\n \”error\”: {\r\n \”code\”: \”ResourceDeploymentFailure\”,\r\n \”message\”: \”The resource operation completed with terminal provisioning state ‘Failed’.\”,\r\n \”details\”: [\r\n {\r\n \”code\”: \”DeploymentFailed\”,\r\n \”message\”: \”At least one resource deployment operation failed. Please list deployment operations for details. Please see https://aka.ms/DeployOperations for usage details.\”,\r\n \”details\”: [\r\n {\r\n \”code\”: \”Conflict\”,\r\n \”message\”: \”{\r\n \\”status\\”: \\”Failed\\”,\r\n \\”error\\”: {\r\n \\”code\\”: \\”ResourceDeploymentFailure\\”,\r\n \\”message\\”: \\”The resource operation completed with terminal provisioning state ‘Failed’.\\”,\r\n \\”details\\”: [\r\n {\r\n \\”code\\”: \\”VMExtensionProvisioningError\\”,\r\n \\”message\\”: \\”VM has reported a failure when processing extension ‘dscextension’. Error message: \\\\”The DSC Extension failed to execute: Error downloading https://wvdportalstorageblob.blob.core.windows.net/galleryartifacts/Configuration_9-11-2020.zip after 29 attempts: Unable to connect to the remote server.\\r\\nMore information about the failure can be found in the logs located under ‘C:\\\\WindowsAzure\\\\Logs\\\\Plugins\\\\Microsoft.Powershell.DSC\\\\2.80.1.0’ on the VM.\\\\”\\r\\n\\r\\nMore information on troubleshooting is available at https://aka.ms/VMExtensionDSCWindowsTroubleshoot \\”\r\n }\r\n ]\r\n }\r\n}\”\r\n },\r\n {\r\n \”code\”: \”Conflict\”,\r\n \”message\”: \”{\r\n \\”status\\”: \\”Failed\\”,\r\n \\”error\\”: {\r\n \\”code\\”: \\”ResourceDeploymentFailure\\”,\r\n \\”message\\”: \\”The resource operation completed with terminal provisioning state ‘Failed’.\\”,\r\n \\”details\\”: [\r\n {\r\n \\”code\\”: \\”VMExtensionProvisioningError\\”,\r\n \\”message\\”: \\”VM has reported a failure when processing extension ‘dscextension’. Error message: \\\\”The DSC Extension failed to execute: Error downloading https://wvdportalstorageblob.blob.core.windows.net/galleryartifacts/Configuration_9-11-2020.zip after 29 attempts: Unable to connect to the remote server.\\r\\nMore information about the failure can be found in the logs located under ‘C:\\\\WindowsAzure\\\\Logs\\\\Plugins\\\\Microsoft.Powershell.DSC\\\\2.80.1.0’ on the VM.\\\\”\\r\\n\\r\\nMore information on troubleshooting is available at https://aka.ms/VMExtensionDSCWindowsTroubleshoot \\”\r\n }\r\n ]\r\n }\r\n}\”\r\n }\r\n ]\r\n }\r\n ]\r\n }\r\n}”}]}
Root Cause:
There was no internet access for the subnet used for host pool creation
Resolution:
Internet connectivity required for WVD VNET as DSC extension need to download from Azure Websites. The DSC extension for Windows requires that the target virtual machine is able to communicate with Azure and the location of the configuration package (.zip file) if it is stored in a location outside of Azure.
Ref: https://docs.microsoft.com/en-us/azure/virtual-machines/extensions/dsc-windows
Issue 2: Unable to create Host pool from Custom Image
Error
{“code”:”DeploymentFailed”,”message”:”At least one resource deployment operation failed. Please list deployment operations for details. Please see https://aka.ms/DeployOperations for usage details.”,”details”:[{“code”:”Conflict”,”message”:”{\r\n \”status\”: \”Failed\”,\r\n \”error\”: {\r\n \”code\”: \”ResourceDeploymentFailure\”,\r\n \”message\”: \”The resource operation completed with terminal provisioning state ‘Failed’.\”,\r\n \”details\”: [\r\n {\r\n \”code\”: \”DeploymentFailed\”,\r\n \”message\”: \”At least one resource deployment operation failed. Please list deployment operations for details. Please see https://aka.ms/DeployOperations for usage details.\”,\r\n \”details\”: [\r\n {\r\n \”code\”: \”Conflict\”,\r\n \”message\”: \”{\r\n \\”status\\”: \\”Failed\\”,\r\n \\”error\\”: {\r\n \\”code\\”: \\”ResourceDeploymentFailure\\”,\r\n \\”message\\”: \\”The resource operation completed with terminal provisioning state ‘Failed’.\\”,\r\n \\”details\\”: [\r\n {\r\n \\”code\\”: \\”VMExtensionProvisioningTimeout\\”,\r\n \\”message\\”: \\”Provisioning of VM extension dscextension has timed out. Extension provisioning has taken too long to complete. The extension did not report a message. More information on troubleshooting is available at https://aka.ms/VMExtensionDSCWindowsTroubleshoot\\”\r\n }\r\n ]\r\n }\r\n}\”\r\n },\r\n {\r\n \”code\”: \”Conflict\”,\r\n \”message\”: \”{\r\n \\”status\\”: \\”Failed\\”,\r\n \\”error\\”: {\r\n \\”code\\”: \\”ResourceDeploymentFailure\\”,\r\n \\”message\\”: \\”The resource operation completed with terminal provisioning state ‘Failed’.\\”,\r\n \\”details\\”: [\r\n {\r\n \\”code\\”: \\”VMExtensionProvisioningTimeout\\”,\r\n \\”message\\”: \\”Provisioning of VM extension dscextension has timed out. Extension provisioning has taken too long to complete. The extension did not report a message. More information on troubleshooting is available at https://aka.ms/VMExtensionDSCWindowsTroubleshoot\\”\r\n }\r\n ]\r\n }\r\n}\”\r\n }\r\n ]\r\n }\r\n ]\r\n }\r\n}”}]
Root Cause
Issue with Image which is captured from existing Host Pool
Resolution
Do not capture image from Hostpool Sessions as this breaks sometimes , always
Take new image from Market Place ->convert to Image ->Create Host pools -> For Host update , again use previous captured image
Issue 3: Host pools are able to create with fresh images but not with applications installed on Image (custom)
Error
{“code”:”DeploymentFailed”,”message”:”At least one resource deployment operation failed. Please list deployment operations for details. Please see https://aka.ms/DeployOperations for usage details.”,”details”:[{“code”:”VMExtensionProvisioningTimeout”,”message”:”Provisioning of VM extension joindomain has timed out. Extension provisioning has taken too long to complete. The extension did not report a message. More information on troubleshooting is available at https://aka.ms/vmextensionwindowstroubleshoot”}]}
Root Cause
Visual studio 2015 & 2017 , customer 3rd part application are blocking to create Host pool – Issue experienced with 2 customers
Resolution
Able to create Hostpools after uninstallation of Visual studio
Windows Virtual Desktop is a service that gives users easy and secure access to their virtualized desktops and RemoteApps. This topic will tell you a bit more about the general structure of the Windows Virtual Desktop environment.
Host pools
A host pool is a collection of Azure virtual machines that register to Windows Virtual Desktop as session hosts when you run the Windows Virtual Desktop agent. All session host virtual machines in a host pool should be sourced from the same image for a consistent user experience.
A host pool can be one of two types:
- Personal, where each session host is assigned to individual users.
- Pooled, where session hosts can accept connections from any user authorized to an app group within the host pool.
You can set additional properties on the host pool to change its load-balancing behavior, how many sessions each session host can take, and what the user can do to session hosts in the host pool while signed in to their Windows Virtual Desktop sessions. You control the resources published to users through app groups.
App groups
An app group is a logical grouping of applications installed on session hosts in the host pool. An app group can be one of two types:
- RemoteApp, where users access the RemoteApps you individually select and publish to the app group
- Desktop, where users access the full desktop
By default, a desktop app group (named “Desktop Application Group”) is automatically created whenever you create a host pool. You can remove this app group at any time. However, you can’t create another desktop app group in the host pool while a desktop app group exists. To publish RemoteApps, you must create a RemoteApp app group. You can create multiple RemoteApp app groups to accommodate different worker scenarios. Different RemoteApp app groups can also contain overlapping RemoteApps.
To publish resources to users, you must assign them to app groups. When assigning users to app groups, consider the following things:
- A user can be assigned to both a desktop app group and a RemoteApp app group in the same host pool. However, users can only launch one type of app group per session. Users can’t launch both types of app groups at the same time in a single session.
- A user can be assigned to multiple app groups within the same host pool, and their feed will be an accumulation of both app groups.
Workspaces
A workspace is a logical grouping of application groups in Windows Virtual Desktop. Each Windows Virtual Desktop application group must be associated with a workspace for users to see the remote apps and desktops published to them.
End users
After you’ve assigned users to their app groups, they can connect to a Windows Virtual Desktop deployment with any of the Windows Virtual Desktop clients.
Microsoft manages the following Windows Virtual Desktop services as part of Azure:

Web Access
The Web Access service within Window Virtual Desktop lets user’s access virtual desktops and remote apps through an HTML5-compatible web browser as they would with a local PC, from anywhere on any device. Web Access is secured for Diageo users using OKTA multifactor authentication.
Gateway
The Remote Connection Gateway service connects remote users to Windows Virtual Desktop apps and desktops from any internet-connected device that can run a Windows Virtual Desktop client. The client connects to a gateway, which then orchestrates a connection from a VM back to the same gateway.
Connection Broker
The Connection Broker service manages WVD user connections to virtual desktops and remote apps. The Connection Broker provides load balancing and reconnection to existing sessions.
Diagnostics
Remote Desktop Diagnostics is an event-based aggregator that marks each user and administrator action on the Windows Virtual Desktop deployment as a success or failure. WVD Administrators can query the event aggregation to identify failing components as per requirements.
Extensibility components
Windows Virtual Desktop includes several extensibility components. Windows Virtual Desktop can be managed using Windows PowerShell or with the provided REST APIs, which also enable support from third-party tools. WVD team is using Azure ARM/GUI for WVD management for this deployment.
WVD User Connection Traffic flow
WVD uses Reverse Connect, which means that no inbound ports need to be opened on the VM to setup the RDP connection. Once the connection flow proceeds, bidirectional communication between session hosts/host pools will go over port https (443).
Windows Virtual Desktop is a global load balanced service via Azure front-door. This means that the traffic flow always goes via the nearest management control-plane/service location.
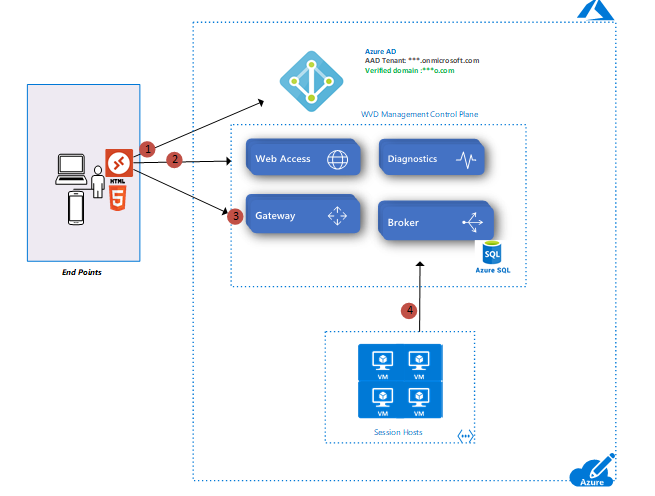
User Connection Flow
- User launches RD client which connects to Azure AD, Azure MFA, user signs in, and Azure AD returns token
- RD client presents token to Web Access, Broker queries DB to determine resources authorized for user
- User selects resource, RD client connects to Gateway
- Broker orchestrates connection from host agent to Gateway
RDP traffic now flows between RD client and session host VM over connections 3 and 4
Guest Post – Thanks to Marius Sandbu for great information
Azure provides internal name resolution for VMs and role instances (including app services) for all services that reside within a virtual network. When setting up a virtual network it will by default use the internal Azure DNS service.
When you setup a virtual machine within this VNET it will automatically get assigned IP by a DHCP service and DNS lookup services by an internal IP address 168.63.129.16. This IP address is an internal VIP address by Microsoft (Which is only available internally from within Azure) https://docs.microsoft.com/en-us/azure/virtual-network/what-is-ip-address-168-63-129-16 (Traffic should not be blocked to this IP address, this address is static and will not change)
You can also change the DNS Server scope on a virtual network, but this will not affect other virtual networks that are peered or otherwise connected to the virtual network using VPN or ExpressRoute.
When it comes to providing DNS Servces in Azure, there are a couple of options.
- Azure built-in DNS (Does not provide any ability to change or update record)
- DNS Server running IaaS (Provides full flexibility, but requires that you have virtual machines that running to deliver DNS services)
- DNS Proxy (Having a virtual machine or service which can provide DNS services for services in Azure but authoritative DNS servers are outside of Azure)
- Azure DNS Private Zones (An internal DNS Service in Azure which can provide DNS lookup within a virtual network, allows you to manage records in Azure)
For more architecture ,download below guide